
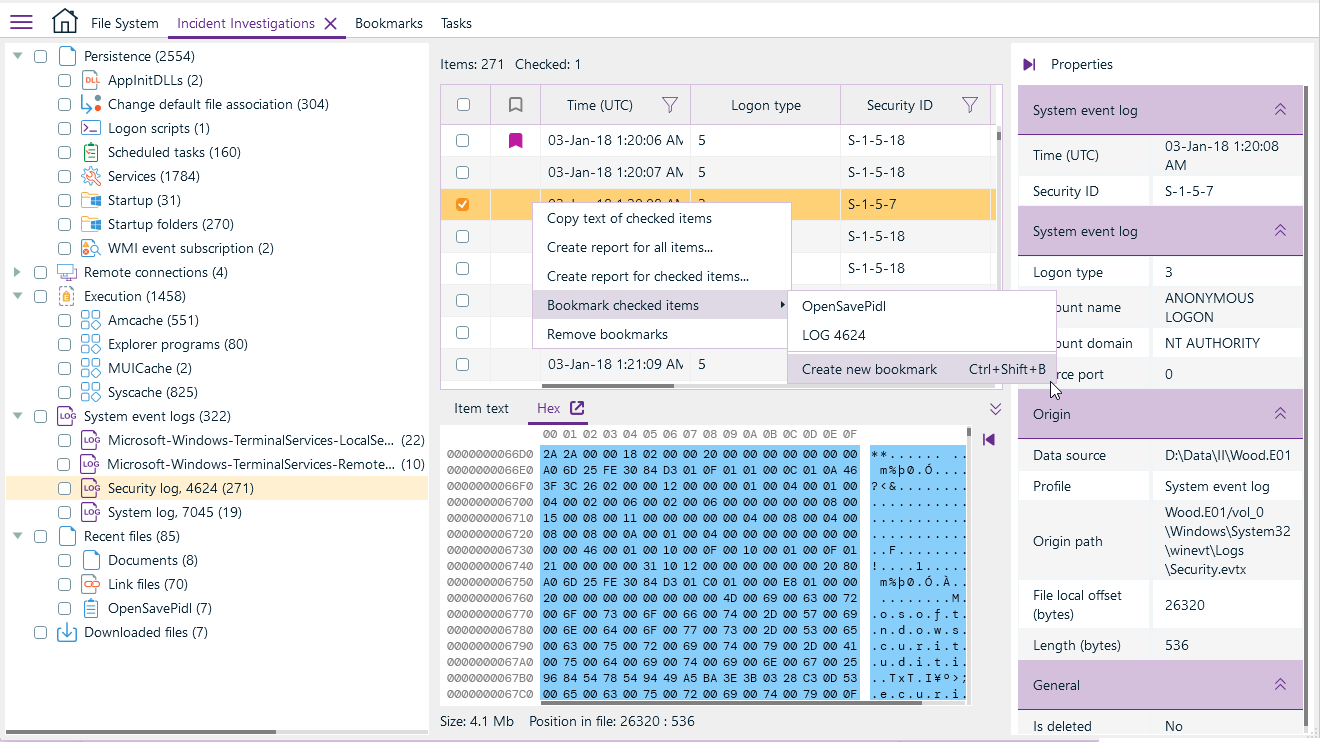
Belkasoft Incident Investigations (Belkasoft N) is a tool for digital incident investigations, developed specifically for businesses and aimed to investigate hacking attempts of Windows-based computers.
By analyzing numerous sources, Belkasoft N can find traces, which are typical for various tricks used by hackers to penetrate company's infrastructure.
Key features

Detect suspicious traces in most typical locations, including registries, event logs and less known files

Analyze how malicious code persisted in the system by analyzing services, scheduled tasks, WMI subscriptions, Applinit DLLs and so on
Learn how and when malware was executed by examining various artifacts such as Amcache and Shimcache, Syscache, BAM and DAM

Extract remote connections details including IP and time stamps for RDP and TeamViewer

Find potential initial attack vector by analyzing recently opened documents and browser links, latest downloads and so on
Search inside extracted information, bookmark important data and create reports in multiple formats
Use cases
Endpoint attacks
Focus on attacks designed to compromise endpoints: phishing e-mails and other attack vectors begin with a compromised PC or laptop.
Malicious email activity
Detect patterns indicating attackers use e-mail services to access the network.
Remote access attacks
Detect misuse of remote access either by outsiders or insiders.
Anomalous user activity
Detect indications of abnormal system usage, abnormal use of credentials, or escalation of credentials.
Attacks correlation with known vulnerabilities
By means of consistent vulnerability scanning correlate attack vectors which can be utilized by malicious users to exploit those vulnerabilities.
Why should you consider Belkasoft N?
Quick
Quickly respond to hacker attacks thanks to all necessary data conveniently presented on a single screen

Comprehensive analysis
Detect impactful security events by analyzing numerous sources, such as registry, event logs, other system files and less known sources

Search, bookmarking and reporting
Search inside found artifacts, bookmark important data and generate comprehensive incident reports right after the analysis stage

Compatibility with the other Belkasoft products
Benefit from the analysis functionality of images acquired by Belkasoft X, Belkasoft R, and Belkasoft T as well as by the third-party tools

Affordable
Comparing to the pricing of the alternative products, it will fit your budget easily

What's next?
CONTACT
NEED ADVICE?
Talk to an expert who can help you to identify the product configuration you need and answer your questions.
Talk to us