Checkm8 Review
The checkm8 exploit for iOS devices emerged in September 2019. It opened new doors for digital forensics researchers and investigators, who are always looking to extract and analyze data from devices. Can I extract data from a blocked or damaged iPhone? Can I find the PIN code of a blocked device? You will find the answers to these questions and more in this article.
The checkm8 exploit for iOS devices emerged in September 2019. It opened new doors for digital forensics researchers and investigators, who are always looking to extract and analyze data from devices.
You will find the answers to these questions and more in this article.
History of jailbreak developments based on the checkm8 exploit
On September 27, 2019, Axi0mX, a Twitter user, presented the Checkm8 exploit to the public. Checkm8 is a vulnerability that compromised information found on millions of Apple devices (from iPhone 4s to iPhone X) .
Axi0mX later deleted his original post, but copies of that post can still be found on the web.
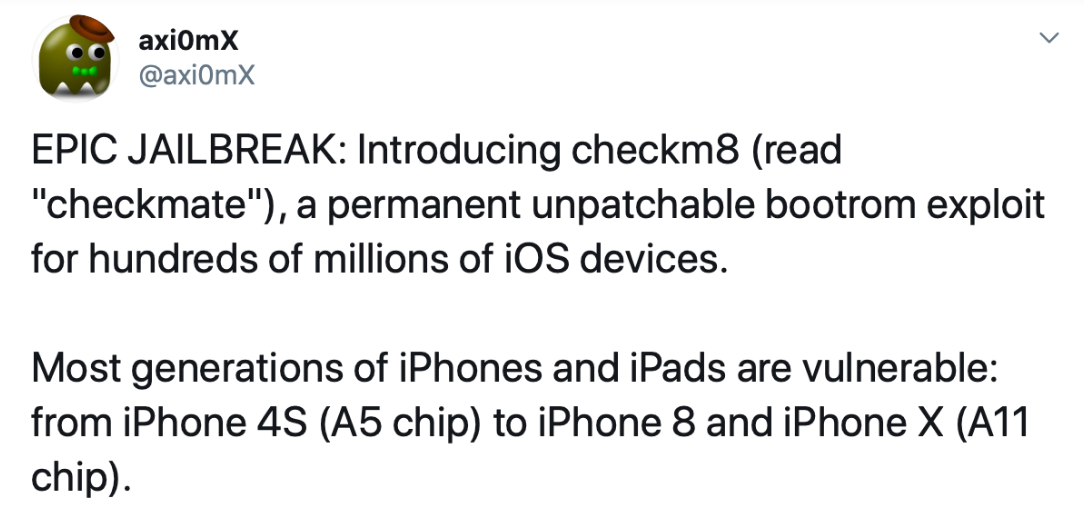
Figure 1. Axi0mX's post on Twitter
After the announcement, several firms (especially those who develop forensic programs for mobile device research) and enthusiasts began developing jailbreaks procedures based on the exploit. Their research was largely successful.
Today, the most popular jailbreaks based on the Checkm8 exploit are Checkra1n and King. Furthermore, proprietary jailbreak procedures—based on the same checkm8 exploit—were also developed. Such procedures are used in premium digital forensic products.