Due to the crisis resulting from the spread of COVID-19, more people are currently working from home than ever.
In this article, we will examine the major security risks confronting organizations, especially those threats exacerbated by recent events.
We will also propose effective mitigation methods involving Belkasoft Evidence Center.
What impact has COVID-19 had on IT infrastructures?
Health, economic, political, and social systems are hardly the only establishments that have been affected by the coronavirus pandemic. The virus also caused disruptions in the digital world.
For example, some of the biggest companies—Facebook, Google, and others—have implemented WFH (work from home) policies for most of their employees all over the world.

Workers are now spending more time on video calls/conferences and chat programs; internet traffic during work hours has increased; some employees are using their home computers to perform official tasks; and so on.
The rise in remote work corresponds to an increase in time spent on the internet. And this change has serious implications for everyone.
While COVID-19 delivers different economic outlooks for organizations, the challenges resulting from the crisis—in terms of security—are the same for everybody.
In fact, in one Europol report, these IT-related developments formed half (2/4) of the major issues.
- Cyberattacks:
- Fraud:
Many security researchers and investigators claim that cybercrimes have increased in recent times.
Cybercriminals are looking to profit through a wide variety of online scams, phishing emails, malicious websites, and harmful applications.

Fraud schemes crafted to capitalize on the fears and concerns of people have also seen a significant increase.
Some employees might also take advantage of the chaos and uncertainty to carry out fraudulent acts.
How can Belkasoft Evidence Center help businesses to mitigate cyberattacks and fraud?
As a digital forensic tool, Belkasoft Evidence Center makes it easy for an investigator to acquire, search, analyze, store, and share digital evidence from computers, smartphones, RAM, and cloud services.
With Belkasoft Evidence Center (BEC), businesses can monitor events and quickly figure out what happened across all evidence sources and information units. This way, they get to identify threats early enough and protect their interests.
Dealing with cyberattacks:
- With the Incident Investigation module in BEC, you can easily investigate hacking attempts into your Windows computers
- Individuals and organizations can use Belkasoft Evidence Center to examine and analyze items from the registry, events logs, and memory dumps
- Belkasoft can find traces of intrusions and tricks, which cybercriminals employ to penetrate firms’ infrastructures
- Belkasoft Evidence Center will bring your attention to changes in default file associations, review scheduled tasks, check remote connections, and peruse critical artifacts.
- You get to review the origin of an attack and find out where malicious code was executed.
Dealing with fraud:
- Before fraud can be investigated, it has to be detected first. By examining the entirety of data stored on a hard drive, you can review events in which data was accessed and determine the people involved.
Cloud-based investigations can also be carried out.
- With Belkasoft Evidence Center, you can gather information on communications involving staff and customers.
- You can find and analyze forensically important artifacts such as emails, documents, call logs, chats, and pictures.
- You can recover deleted data ranging from deleted files (and folders) to cleaned WhatsApp, Skype, and (hundreds of) other messaging-applications chats.
Even destroyed evidence remains within your reach.
- With Belkasoft Evidence Center, you get to figure out the fraudsters or employees—who took advantage of their privileged access to alter records or hide files—for financial gain.
Using Remote Acquisition
Remote acquisition refers to any process that facilitates the gathering of digital evidence from a device without physical interactions. Remote acquisition is a critical component of remote forensics, even now more so than ever.
Since employees rarely do their work in offices these days due to the COVID-19 crisis, businesses find it difficult to monitor, extract, and gather data from their computers. The remote acquisition function in BEC is an incredibly valuable resource in this regard.
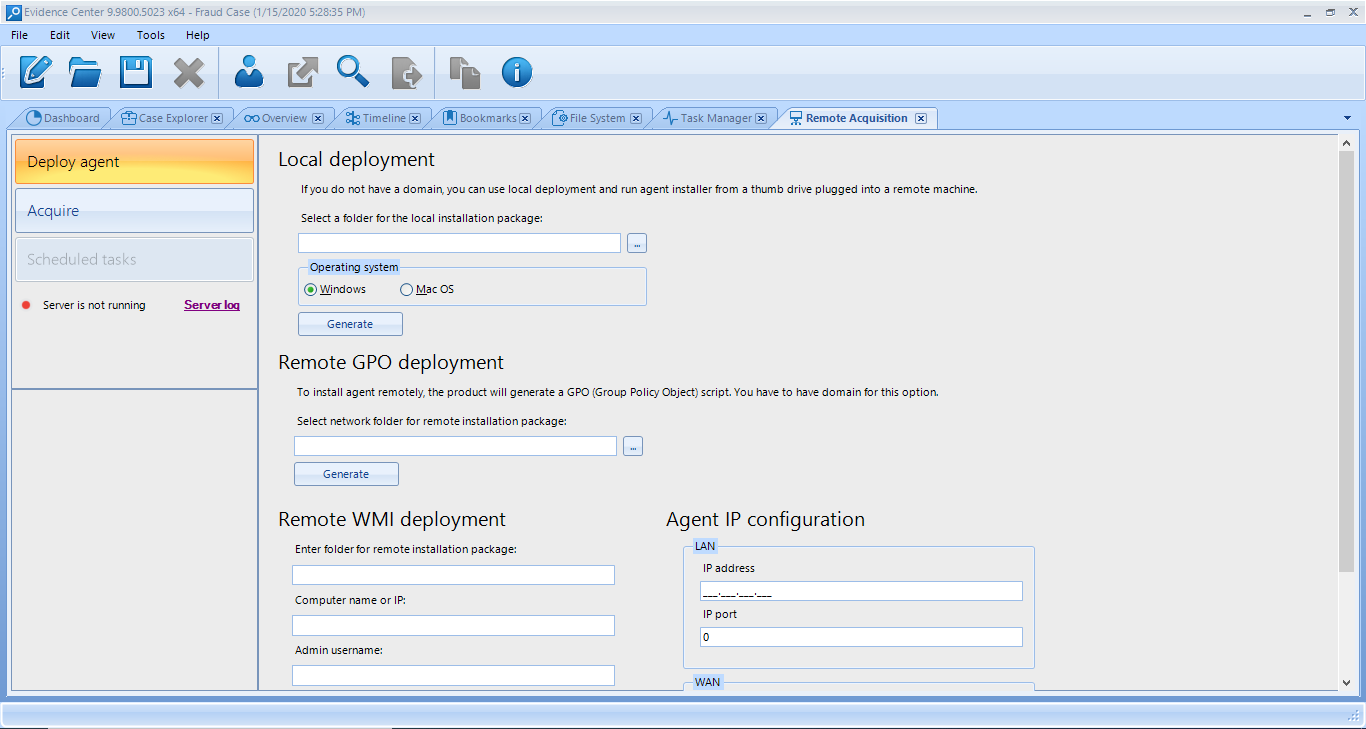
In general, Belkasoft supports remote acquisition of data from
- Hard drives in computers (Windows and macOS)
- Removable drives
- Volatile memory (RAM) in computers (Windows)
- Mobile devices (connected remotely to a Windows machine)
Through remote acquisition, you get to review your employees’ communications and correspondences (emails and chats, for example) and monitor changes in records (documents and files, for example). And most importantly, you get to do all this from the comfort of your home, which is probably your workplace these days.
Remote forensics—with Belkasoft Evidence Center—covers a wide variety of forensic approaches used to extract and analyze data. You can use BEC to perform computer forensics remotely in an enterprise environment.
For example, you get to obtain full device images of your corporate workstations and servers. Your organization having one office or several workplaces hardly matters here. Your staff works from home? No worries!
Conclusion
While the COVID-19 crisis presented unforeseen and difficult problems for all kinds of firms, managers can (and must) still find ways to make things work. As a general rule, businesses try to mitigate risks and make the right decisions to protect their interests.
Remote forensics and incident response—powered by remote acquisition and other top-level functions in Belkasoft Evidence Center—provides a clear path through which you get to collect and analyze evidence from several data sources in a convenient manner. This way, you get to significantly reduce the chances of financial loss resulting from cyberattacks and fraud.
Read more Belkasoft articles on checkm8 and other digital forensic issues at https://belkasoft.com/articles.
Download the trial version of Belkasoft Evidence Center at https://belkasoft.com/trial.
Request a quote at https://belkasoft.com/quote.