Temporal analysis of events (Timeline) can be beneficial when you want to reconstruct events related to computer incidents, data breaches, or virus attacks taking place on a victim’s computer.
Historically, digital forensic timeline analysis has been broken down into two parts:
- ‘Timeline’ to describe changes associated with temporal file metadata in a file system. In other words, this Timeline is based exclusively on the corresponding file system.
- ‘Super Timeline’ to describe changes associated with temporal metadata for the maximum number of artifacts possible within both file system and operating system. That is to say, it combines data from both sources.
However, some time ago Microsoft introduced a new type of Windows artifact: Windows 10 Timeline. It offers new opportunities to investigators, with greater clarity. This article describes these new forensic capabilities with Windows 10 Timeline.
Windows 10 Timeline
The April 2018 Windows 10 update introduced a new feature called ‘Timeline.’ It enables you to look through a computer user’s activities and to quickly return to previously opened documents, launched programs, and viewed videos and pictures. To open Windows 10 Timeline, you need to click on an icon located next to the magnifying glass icon, i.e., Task View (or click WinKey + Tab).
After that, thumbnails of programs/documents/sites that have been opened today or some time ago will become available.
Investigators have identified the following two issues related to this feature:
- Some apps are not displayed in ‘Timeline’ after being opened.
- Some data from ‘Timeline’ (earlier data) is transferred to Microsoft Cloud.
Thus, data obtained via Windows 10 Timeline artifact analysis differs from a customary Timeline and Super Timeline analysis.
Also, Windows 10 Timeline should not be confused with a timeline generated by forensic utility programs. For example, Timeline created by Belkasoft Evidence Center X (Belkasoft X) contains many more entries in comparison with Windows 10 Timeline.
Location of Windows 10 Timeline Database
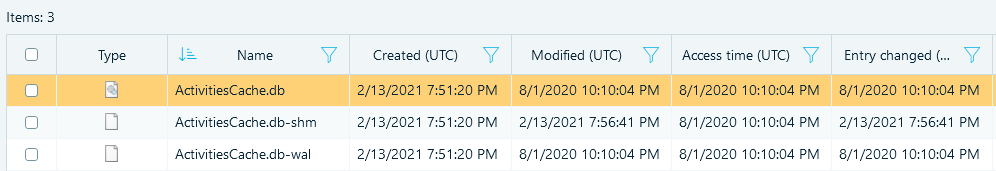
Windows 10 Timeline info covering user activities is stored in the ‘ActivitiesCache.db’ file with the following path:
C:\Users\%profile name%\AppData\Local\ConnectedDevicesPlatform\L.%profile name%\
The ‘ActivitiesCache.db’ file is an SQLite database (ver. 3). Just like any other SQLite database, it is characterized by the following two auxiliary files: ‘ActivitiesCache.db-shm’ and ‘ActivitiesCache.db-wal’.
Additional info about deleted records in an SQL database can be obtained via analyzing unallocated space of the database, in freelists and the WAL-file. Examining them for your forensic analysis may increase the volume of your extracted data by 30%. If you would like to learn more about SQLite database analysis, you can read more in our article ‘Forensic Analysis of SQLite Databases: Free Lists, Write Ahead Log, Unallocated Space and Carving’ available here.
Windows 10 Timeline Anatomy
‘ActivitiesCache.db’ contains the following tables: ‘Activity’, ‘Activity_PackageId’, ‘ActivityAssetCache’, ‘ActivityOperation’, ‘AppSettings’, ‘ManualSequence’, ‘Metadata’.
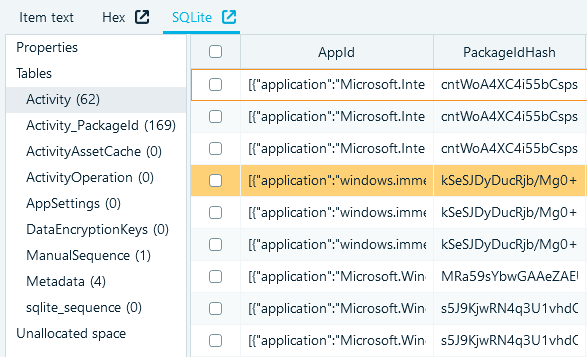
The ‘Activity_PackageId’ and ‘Activity’ tables are of the most significant interest to investigators.
‘Activity_PackageId’ Table
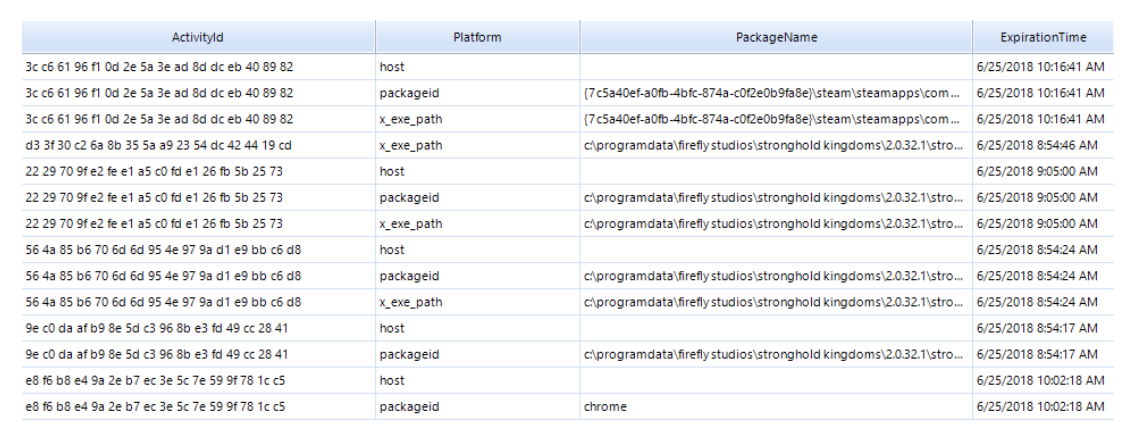
The ‘Activity_PackageId’ table contains records for applications, including paths for executable files. Here is an example string copied from the database:
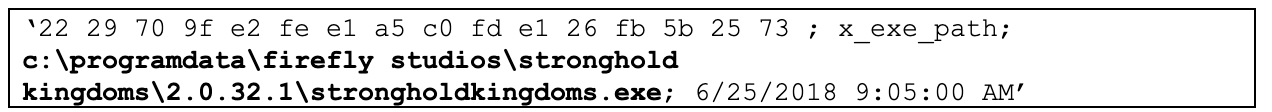
You can also find names of executable files as well as expiration time for these records. Values located in the ‘Expiration Time’ column define a moment when the records covering PC user activities will be deleted from this database. They are stored in the ‘Epoch Time’ format.
The records in the ‘Activity_PackageId’ table are stored for a certain period of time. It may cover records for the previous 30 days. There can be records related to executable files or documents that are not already present on a hard drive being investigated.
‘Activity’ Table
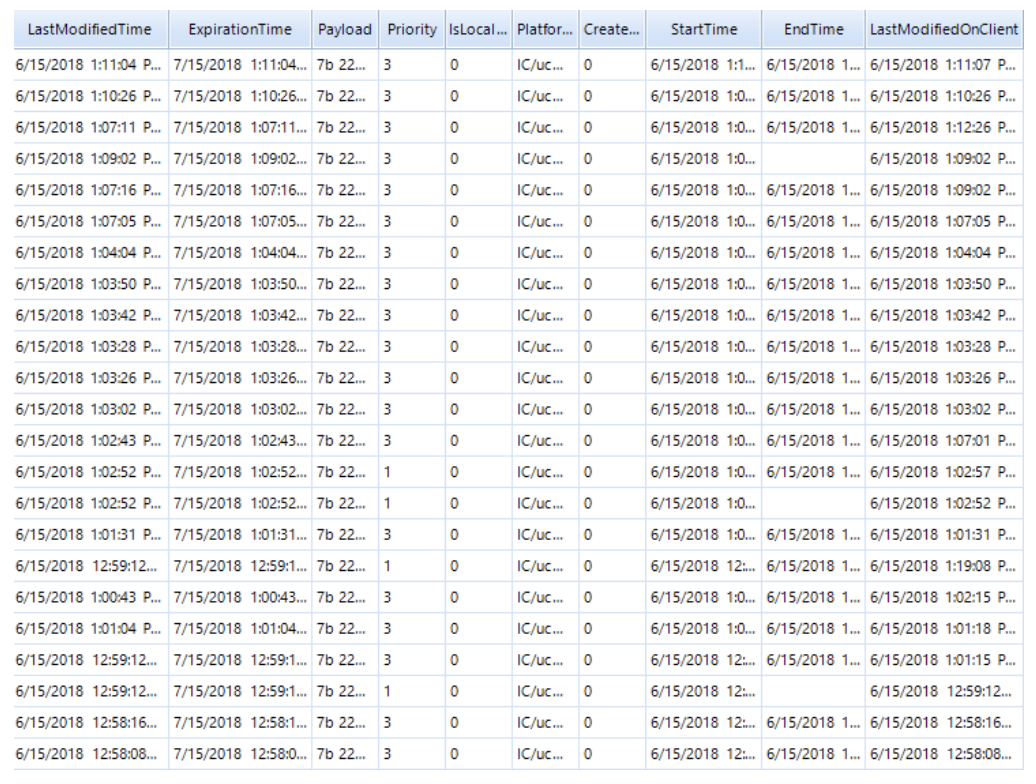
This contains as many as five fields for time tags!
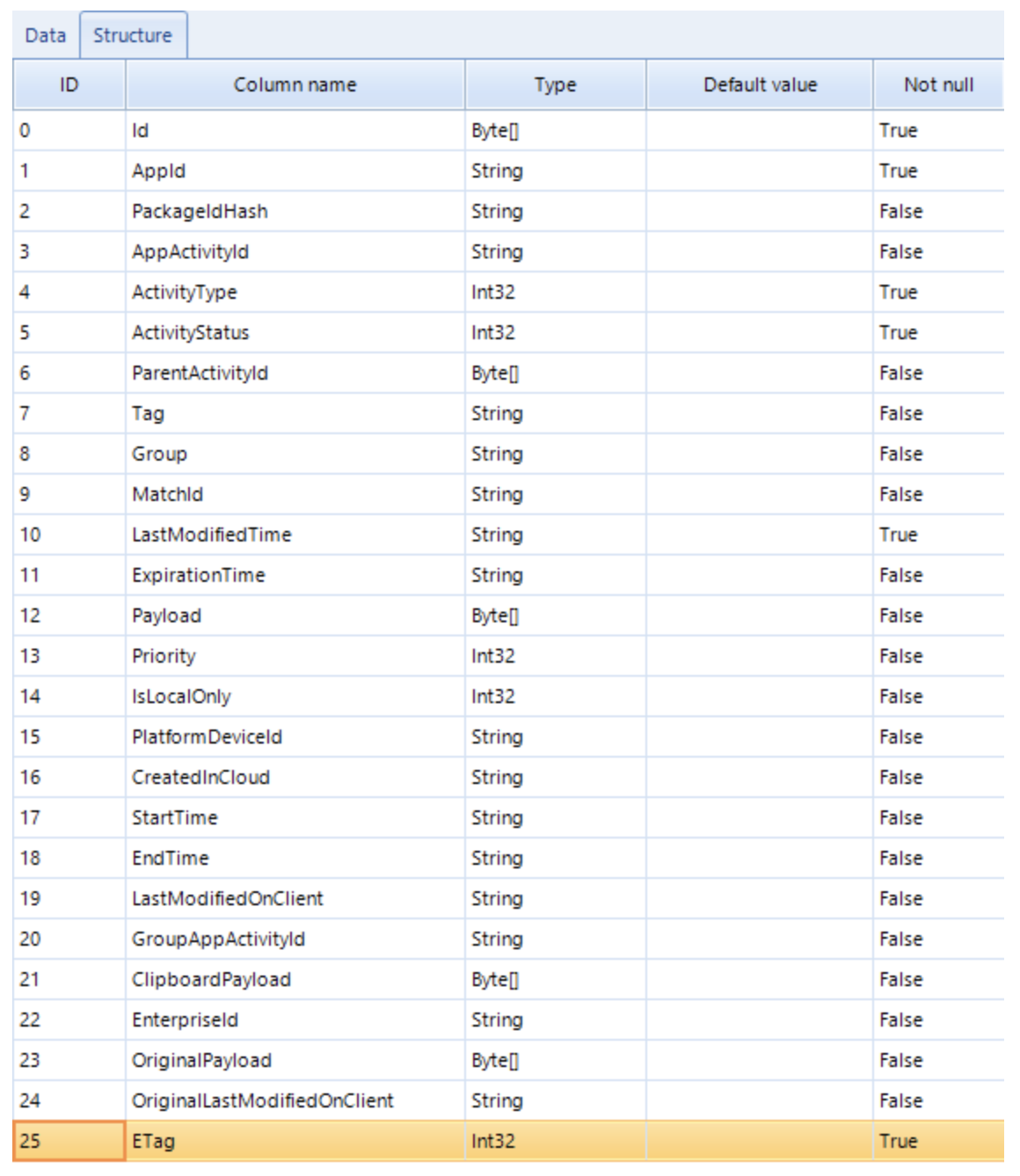
These are LastModifiedTime, ExpirationTime, StartTime, EndTime, LastModifiedOnClient. Their meanings are as follows (datetime in UTC):
- ‘StartTime’ means the moment when an application was launched.
- ‘EndTime’ means the moment when an application ceases to be used.
- ‘ExpirationTime’ means the moment when the storage duration for a record covering a user activity expires in the database.
- LastModifiedTime means the moment when a record covering a PC user activity has been last modified (if such an activity has been repeated several times).
- LastModifiedOnClient may be empty. It is filled out only when users themselves modify files.
- TeamViewer—a program used for remote computer control
- Mimikatz—a program used to steal user identity data
- RDPWrap—a library making it possible for several users to connect to a computer via the RDP protocol.
You can also find paths to the executable files in this table:
‘…:”F:\\NirSoft\\x64\\USBDeview.exe“…’.
Gary Hunter ( @pr3cur50r) stresses in his article ‘Windows 10 Timeline – Initial Review of Forensic Artefacts’ that values of time tags for deleted files do not change. As for modified documents, the volumes of time tags do not change instantly, but within 24 hours.
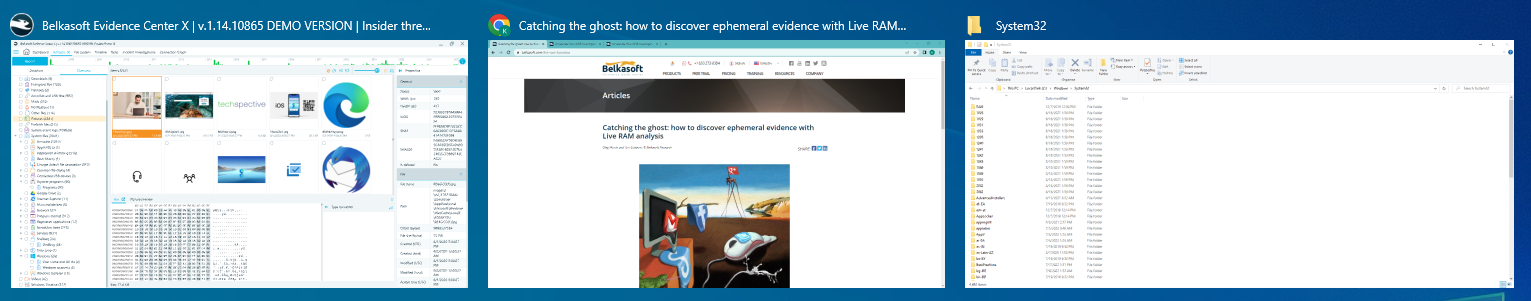
How to Investigate Windows 10 Timeline with Belkasoft X
Once you have added a data source (a hard drive, a logical drive, a folder or a file), select ‘Windows Timeline’ in the ‘System Files’ of the ‘Add data source’ window.
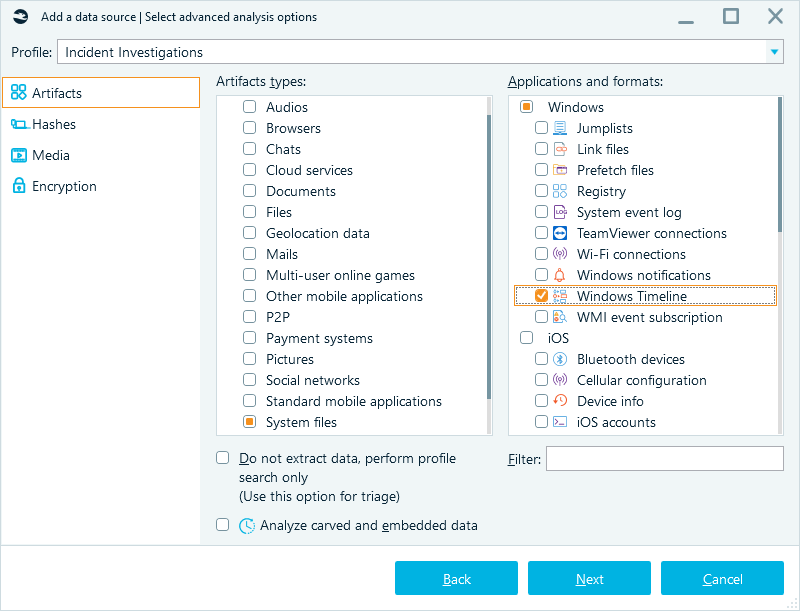
Once you have your data extraction process completed, the ‘Windows Timeline’ category will be displayed in your ‘Overview.’ Data extraction results from the ‘ActivitiesCache.db’ will be shown there.
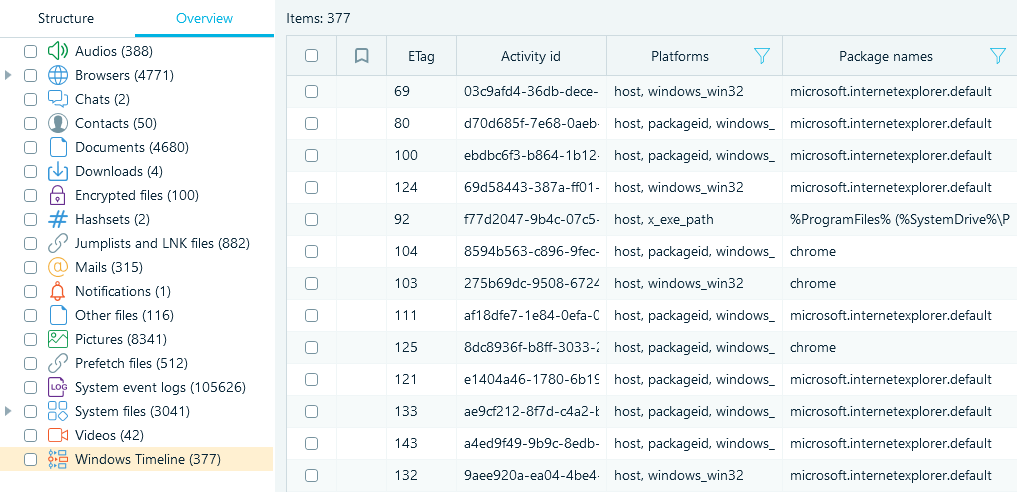
Since the ‘ActivitiesCache.db’ file is an SQLite database, Belkasoft X is capable of restoring deleted records saved in this file and of extracting additional info from the transaction file (WAL-file).
Using Windows 10 Timeline in Computer Forensics
Data contained in Windows 10 Timeline may be used for issues related to incident response and data breaches.
We will show a data fragment of the ‘ActivitiesCache.db’ file from a computer attacked by hackers as an example.
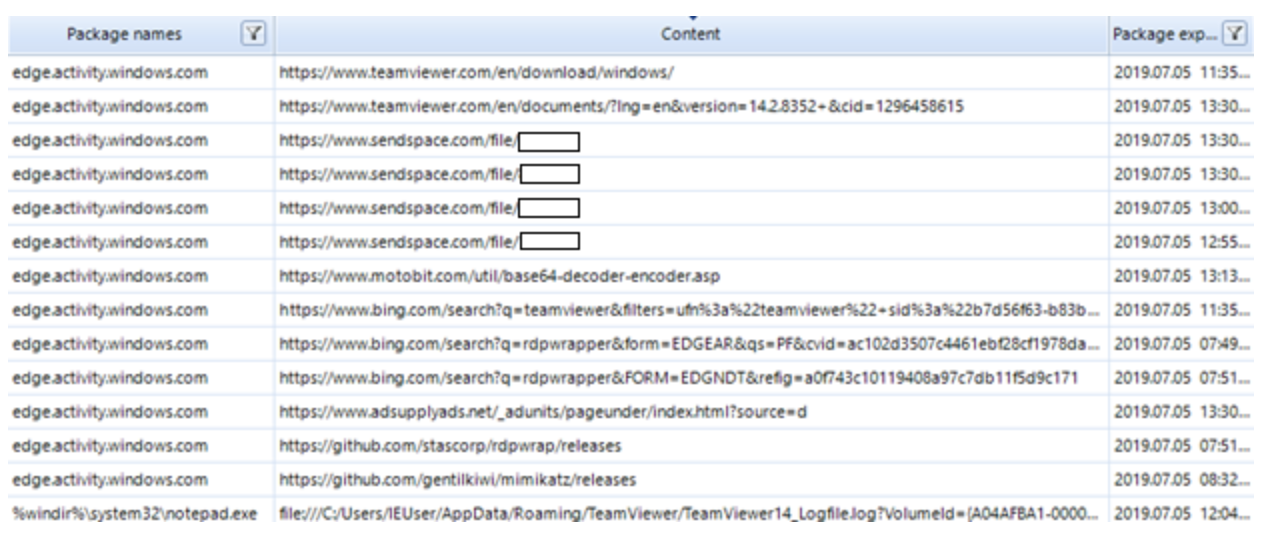
As you can see in the screenshot below, the attackers installed some files on the victim’s computer.
Among other things, the following programs were installed:
More than that, analysis of the events stored in Windows 10 Timeline indicates that the attackers opened the TeamViewer journal of logs (TeamViewer14_Logfile.log file) via Notepad (notepad.exe file). They might have done this to delete or modify the file’s info.
A more convenient search for info across the base being analyzed is available with the Belkasoft X built-in filters.
For example, one could perform sorting based on executable file names (‘Package Name’).
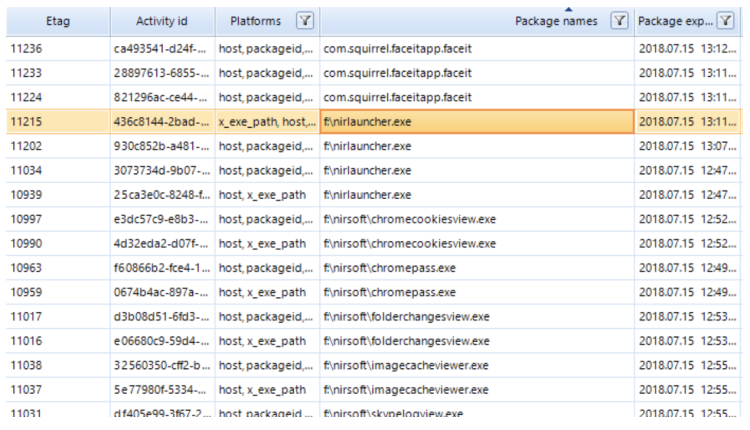
As you can see in the screenshot, the following files were launched on the investigated computer: nirlauncher.exe, chromecookiesview.exe, chromepass.exe, folderchangeview.exe, imagecacheviewer.exe, skypelogview.exe. Looks intriguing!
To locate Microsoft Word-related events, let us enter a search word, namely ‘word’, in the filter panel:
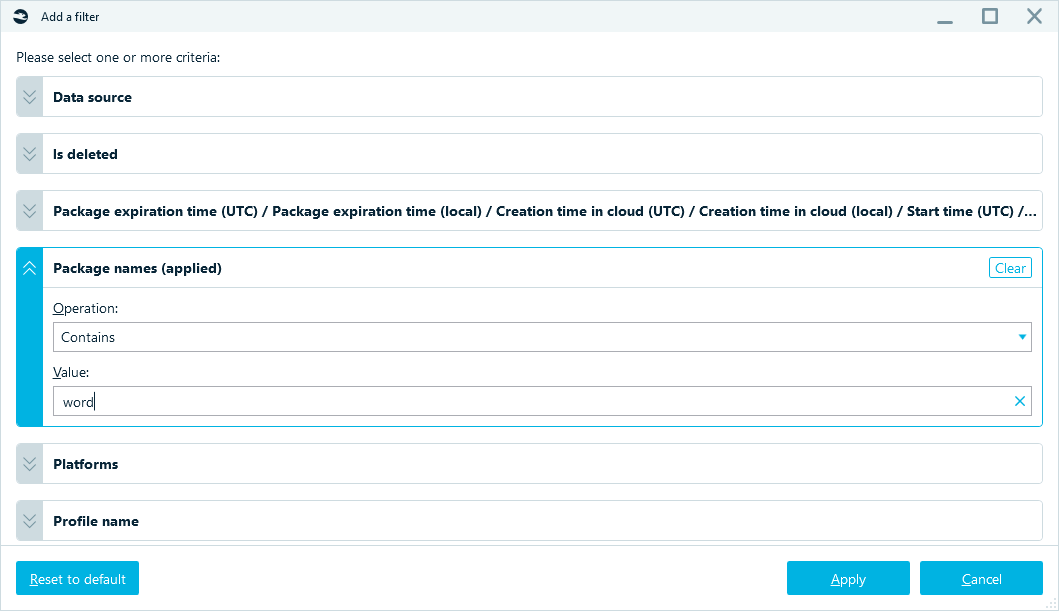
Once we have used the filter, we can find info about the launch of the ‘winword.exe’ executable file in the sorted results.
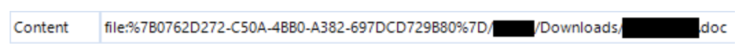
One can also find info about the files that were opened or edited via Microsoft Word by inspecting the timeline event property named ‘Content”:
Conclusion
Windows 10 Timeline significantly facilitates investigative activities aimed at reconstructing the events that have taken place on an investigated computer over the previous 30 days.
More than that, Windows 10 Timeline may provide additional info about the files that have launched on the examined computer, including the deleted ones. This is of particular importance when it comes to incident response and data breaches.
Of course, a reliable tool is needed for such investigations based on Windows 10 Timeline artifacts. Belkasoft Evidence Center X can help you with these types of investigations. With Belkasoft X’s automated search, recovering option for deleted events, analysis of transaction files and SQLite unallocated, and advanced filters at your disposal, your digital forensics or incident response investigation will be much more efficient.