The Investigator’s Guide to Android Acquisition Methods. Part I: Device
Introduction
Android devices come in various brands and models, featuring different chipsets and operating system flavors. This diversity poses challenges when you acquire them as a source of evidence in digital forensics and cyber incident response (DFIR) investigations. Despite the open-source architecture of Android, which provides advanced ways to interact with devices, ongoing enhancements in OS and application security create additional complexities.
Most modern mobile devices are equipped with File-Based Encryption (FBE), a security feature that protects each file using a unique key derived from user credentials and the device hardware keys. This encryption level significantly complicates the extraction of device contents through physical acquisition, once considered the most efficient method. While you can still use physical acquisition on older Android devices, for FBE-protected ones, you can choose methods that obtain unencrypted system and application files.
To successfully acquire mobile devices, it is important to understand device and software specifics. This knowledge helps you assess the possibilities and risks of different methods and organize your investigative tasks accordingly.
In this article, we will explore Android device acquisition methods available in Belkasoft X, arranged from the safest to riskier ones, and cover the following aspects of their usage:
- How the method works
- Which devices it supports
- Data you can expect to obtain with it
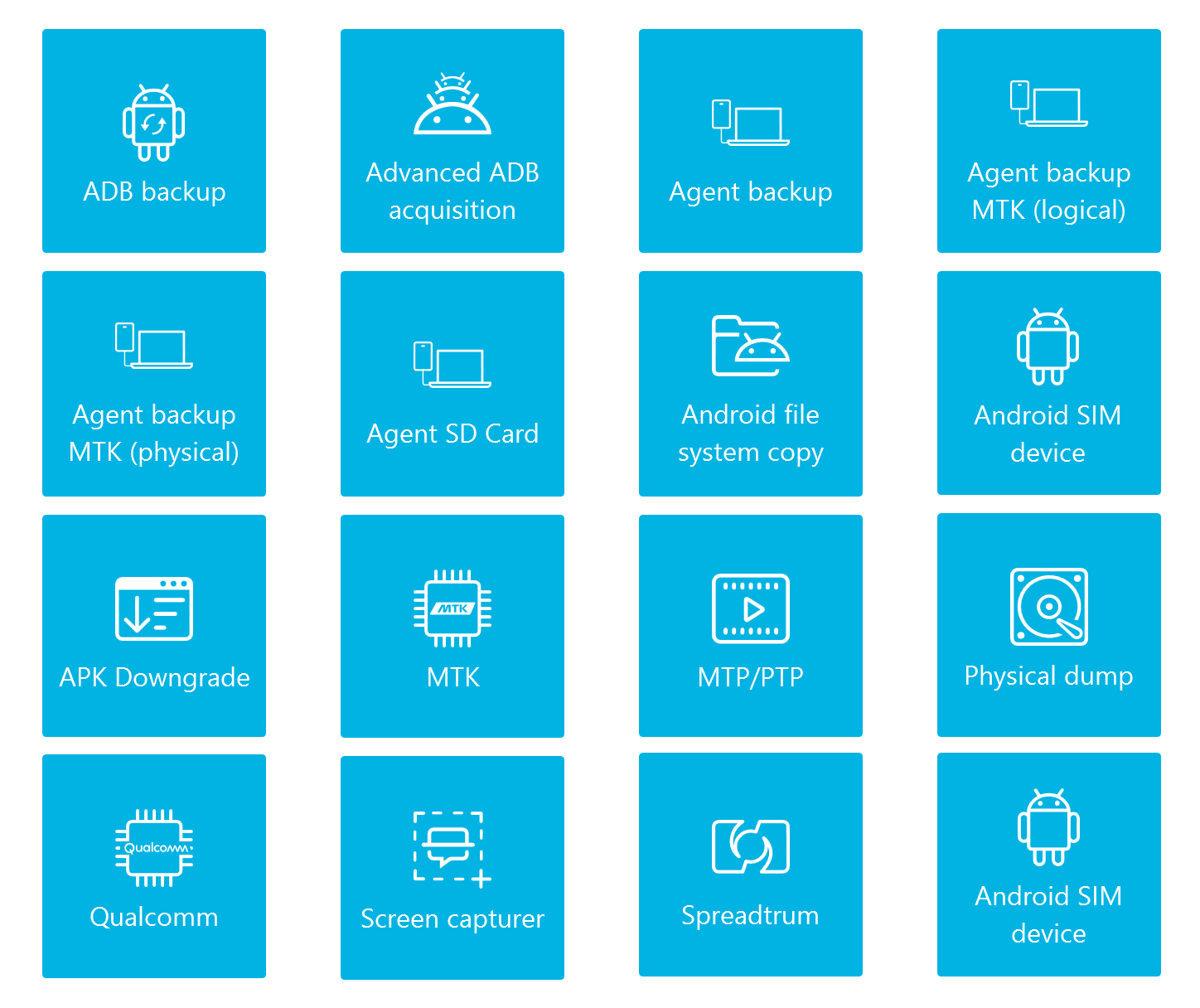
Automated screen capture
Screen capturing allows you to obtain evidence in graphic format. This format may not be as convenient for analysis as forensic images, but it has a number of advantages:
- It employs the least invasive method and works on most devices
- It enables access to data that may not be available if you cannot use advanced acquisition methods on a device
- It can be useful for comparing device on-screen content to data in other forensic images
Manual screen capturing may not be considered forensically sound because it involves saving screenshots to the device internal memory, while it can also be quite time-consuming and error-prone. Belkasoft's Android screen capturer facilitates this task. This method can take fully automated screenshots of popular messengers (WhatsApp, Telegram, Signal) and scroll through other applications, capturing their screens one by one.
When analyzing screenshots from supported messengers, Belkasoft X uses text recognition algorithms to reconstruct captured chats. The results are conveniently displayed in text format under the messenger profile in the Artifacts window.
File copy via MTP and PTP protocols
Media Transfer Protocol (MTP) and Picture Transfer Protocol (PTP) are standard communication protocols used to transfer files between a device and a computer over USB. While PTP is limited to interacting with graphic formats, MTP allows sending and receiving various types of media files.
Belkasoft X provides the MTP/PTP acquisition method that copies Android device files available through these protocols. The files can include pictures, audio and video files, and other document types, such as PDFs. Since MTP and PTP are standard protocols, this method will work for most Android devices.
SIM card acquisition
SIM cards typically include cellular data, such as the mobile subscriber's ID (IMSI) and phone number. They may also contain contact records and SMS texts if the device owner chooses to store them on the SIM card.
You can use the Android SIM device method in Belkasoft X to acquire this information from SIM cards within Android devices. Alternatively, you can use the SIM Reader method to acquire SIM data through a SIM card reader device.
ADB backup acquisition
Android Debug Bridge (ADB) is a tool designed for communicating with Android devices through commands. Among its functionalities is the "backup" command. Belkasoft X employs it to provide the ADB backup acquisition method, allowing you to copy backup files from a wide array of Android devices.
Through this method, you can typically obtain media files, SMS, calendar records, application data, and other artifacts stored within the device internal memory and on SD cards. The amount of files you can obtain may vary based on the settings of the applications installed on the device since the extent of data saved through this mechanism is determined by the application developers.
Agent-based acquisition
In the context of device acquisition, an agent stands for an application that collects data within the device and transfers it to a specific location.
When you use the Agent backup acquisition method in Belkasoft X, the tool installs the agent application on the device you are acquiring to copy its files via USB. When the acquisition is complete, Belkasoft X automatically uninstalls the agent. The information you obtain typically includes contacts, SMS, calendar records, the list of installed applications, and more. The extent of data depends on the device chipset vendor.
One more agent-based method you can use with Belkasoft X is Agent SD card. It allows you to extract files without connecting the device to the workstation with USB. Instead, you use an SD card to copy and deploy the Belkasoft agent onto a device, subsequently exporting data to the same card.
Advanced ADB acquisition
The Advanced ADB acquisition method performs several tasks in one run
- Performs an ADB backup
- Creates an agent backup
- Copies data from the SIM card
The resulting image will include all data you can acquire with these three methods when running them separately.
Chipset-based methods
Acquisition mechanisms depend not only on the operating system but also on the device hardware. In particular, the chipset plays a significant role. Belkasoft X provides a number of chipset-specific acquisition methods to accommodate this challenge.
MediaTek
You can use the following methods to acquire devices powered by MediaTek (MTK) chipsets:
- MTK enables you to acquire physical images of MTK-based devices using Preloader mode; you can find the list of chipsets supported by this method in the Belkasoft X User Reference document
- Agent backup MTK (physical) and Agent backup MTK (logical) help you extract the physical and logical device images using an agent designed to acquire data from MTK-based devices. This method supports more than 150 devices and 25 chipsets, including various models of Huawei, Lenovo, LG, Meizu, Sony, ZTE, and others.
Qualcomm
With the Qualcomm acquisition method, Belkasoft X allows you to acquire a physical image of Android devices running on the Qualcomm Snapdragon chipsets and not protected with File-Based Encryption. This method is based on the emergency download mode (EDL).
The list of supported devices includes more than 250 smartphone models, covering various models of Samsung, Xiaomi, Meizu, ZTE, Vivo, and others.
Spreadtrum
The Spreadtrum acquisition method helps you extract the physical image of Spreadtrum-based Android devices that are not protected with File-Based Encryption.
The method supports 90 phone models, including various models of Archos, ARK, BLU, Intex, Micromax, and others.
APK downgrade
Android Package or APK is the standard Android operating system format for installing applications. Modern-day mobile applications use security mechanisms and encryption to protect their data from direct access within the device. However, in earlier versions of many applications, these measures were not in place. The APK downgrade method in Belkasoft X is based on this catch.
When you use this method, the tool replaces application packages on the device with their earlier versions, which enables it to extract the folders and files with the available data from the downgraded applications, including the files stored on SD cards. Upon completing the acquisition process, Belkasoft X restores the original versions of applications, even in cases where errors occur during the procedure.
This method is on the riskier end since it involves interfering with device software. It may cause logging out of application accounts and loss of some data, so you must use it after obtaining data with other possible methods.
Belkasoft X supports the downgrade and acquisition of multiple Android applications, including Facebook Messenger, Instagram, KakaoTalk, Opera, Signal, Skype, Telegram, Twitter, Viber, WeChat, WhatsApp, Zello, and others.
Android file system copy
The Android file system copy method can help you extract the most comprehensive data set from Android devices, including system files, application files, and many other valuable artifacts. However, it only works on rooted devices.
You can check whether a seized device is rooted in the Settings. In the search bar, type "phone status" and select the related result. If the Phone status displays as Official, you are dealing with an unrooted device. Other values, for example, Custom, indicate that the device is rooted.
The file system copy method is generally safe for already rooted devices, but if you decide to perform rooting yourself, it may cause bricking of the device and complete loss of data. That is why this method is at the end of our list.
Physical dump
The last on our list is the Physical dump method. It enables you to extract the full physical image of rooted Android devices. A physical image provides the most complete dataset when acquired from older devices that are not protected with File-Based Encryption.
Conclusion
There are various Android acquisition methods differing in safety, complexity, focus, and data retrieval capabilities. When acquiring a device with Belkasoft X, you can begin with safer methods like screen capturer, file copy, and ADB backup. Then, you can work up to advanced ones like APK downgrade. For older devices without File-Based Encryption (FBE), you can use chipset-specific physical acquisition methods.
This approach helps customize your strategy based on the device, ensuring a thorough and secure acquisition process.