Mobile Forensics Software: Why Belkasoft X Should Be Your Tool of Choice
Table of Contents
- Mobile Forensics Software: An Introduction to Belkasoft's Leading Solutions
- Belkasoft X
- Belkasoft R
- Overview of Belkasoft's support for mobile forensics
- iOS acquisition support
- Android acquisition support
- SIM-card cloning
- Cloud forensics
- Mobile application analysis
- Benefits of Belkasoft's solutions for mobile forensics
- Ready to test Belkasoft?
- See also
Mobile Forensics Software: An Introduction to Belkasoft's Leading Solutions
Established more than 10 years ago, Belkasoft was primarily famous for its computer forensics tools. However, within the last few years, many DFIR professionals began to choose Belkasoft products specifically for our mobile device forensics and analysis functionality. Belkasoft, along with Cellebrite, was one of the two first companies in the world to support the Checkm8-based full file system iOS acquisition on a Windows platform—while most competitors were 6 to 12 months behind with this feature. It was just one of the reasons for the rising popularity of Belkasoft as a mobile forensics tool. Its solid reputation in phone forensics has made it a go-to solution for many investigators across the globe.
In this article, we will talk about the capabilities of the Belkasoft X mobile forensics software and explore why Belkasoft products should be your primary tools for mobile phone and tablet forensics, both in digital forensics and incident response investigations.
Belkasoft X
Belkasoft X (Belkasoft Evidence Center X) is a flagship tool by Belkasoft for computer, mobile, drone, car, and cloud forensics. It can help you acquire and analyze a wide range of mobile devices, run various analytical tasks, perform case-wide searches, bookmark artifacts, and create reports. Belkasoft X’s versatile functionality makes it ideal for mobile device forensics, helping specialists gather essential data. A free trial of this tool is available at https://belkasoft.com/trial.
Belkasoft R
Belkasoft R (Belkasoft Remote Acquisition) is part of Belkasoft X Corporate. It is a tool for forensically sound remote acquisitions of various types of devices, as well as partial images, including selected artifacts only (e.g., for compliance or eDiscovery needs). This product has a unique capability that allows for the acquisition of mobile devices to be conducted remotely, which adds value to mobile device forensics workflows. A free trial of Belkasoft X Corporate is available at https://belkasoft.com/x-corporate-editions.
Overview of Belkasoft's support for mobile forensics
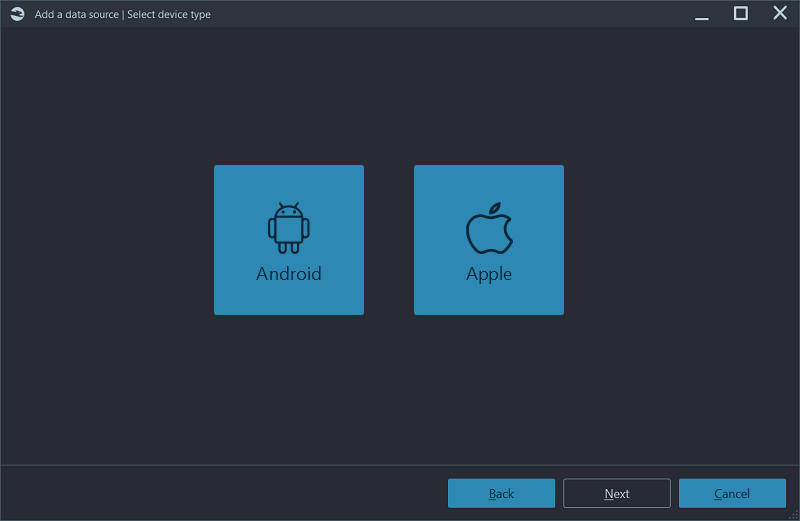
One of the first steps—and the most important one—of working with a mobile device is data acquisition. If no data is acquired, there is nothing to analyze. Belkasoft X has solid support for the acquisition of modern portable devices, including smartphones and tablets, which makes it an indispensable tool for mobile device forensics.
Belkasoft X supports multiple types of acquisitions for both of the most widespread platforms: iOS-based and Android-based devices. It also supports Microsoft (Windows) phones, but since they are no longer produced, we will not review this feature.
Both iOS and Android devices have their peculiarities when it comes to data acquisition. There is a standard backup mechanism for both: iTunes for iOS and ADB for Android. Also, AFC and MTP/PTP protocols allow for media file extraction. However, both iTunes and ADB are very limited in the volume of information provided. When you need to obtain a more comprehensive image, such as the device file system, the available methods are usually not approved by device manufacturers as they involve rooting, jailbreaks, exploits, and other tricks. Many of these methods are device- or chipset-specific.
This is why, for mobile phone forensics, it is important to have multiple types of acquisition available in your tool. This way, you can start with more straightforward methods to be on the safe side.
One of the great features of Belkasoft X is that it allows you to start with the least intrusive and safest methods and continue with more comprehensive (but riskier) ones—making it an invaluable tool in mobile device forensics.
iOS acquisition support
For iOS, Belkasoft X supports the iTunes backup acquisition, including an interesting feature of using lockdown files to avoid unlocking the device in case a passcode is unknown. You can also acquire media files using the Apple File Conduit (AFC) protocol. One more important feature of Belkasoft X is its ability to brute-force unknown passcodes for a range of iOS devices, a critical function in phone forensics.
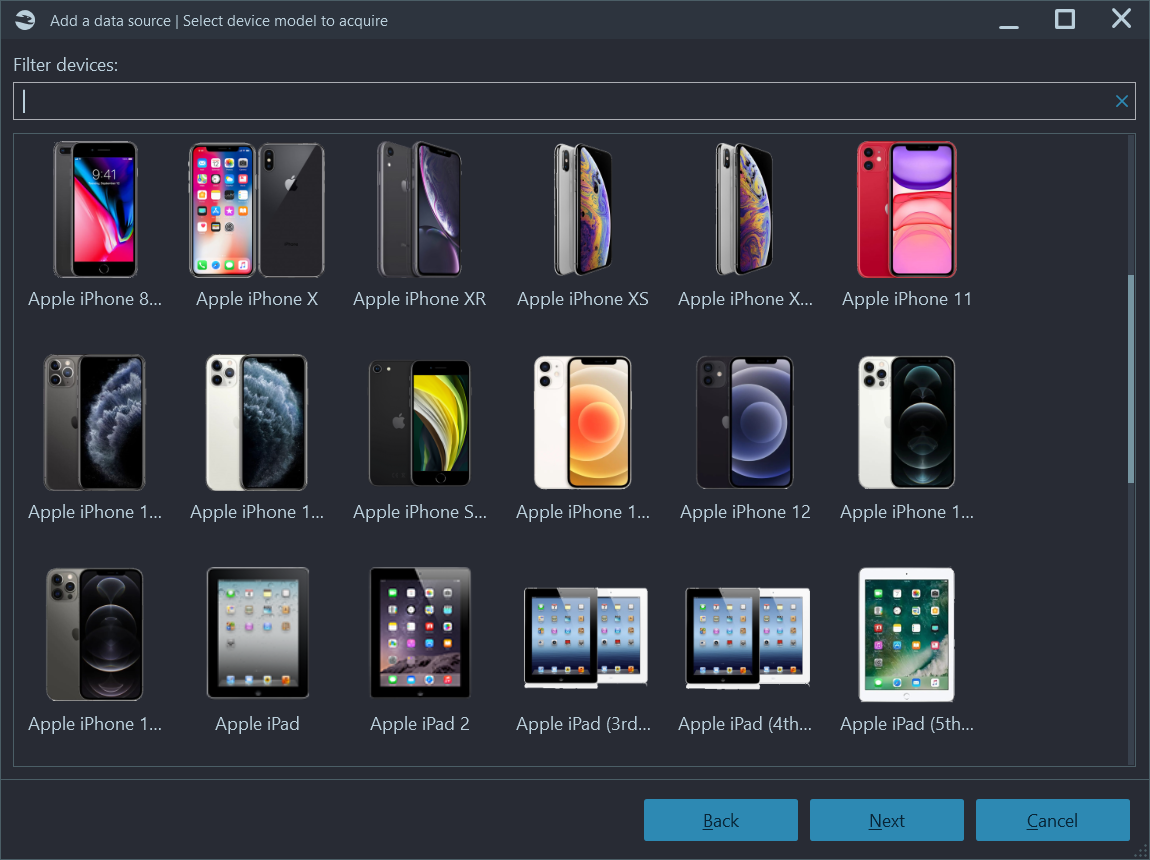
More interestingly, a full file system and even the keychain (password built-in storage) can be acquired with the help of more sophisticated methods such as a jailbroken iPhone/iPad acquisition, Checkm8-based acquisition, and even our agent-based acquisition. To clarify, neither our Checkm8 nor agent-based acquisition is a jailbreak, so they are much more forensically sound ways to acquire data—since, in many countries, it is legally impossible to perform a jailbreak on evidence sources. These methods are integral to mobile device forensics, where secure data acquisition is paramount.
Our agent-based acquisition is just another one of Belkasoft X's benefits, recognized by many customers. There are not many tools on the market that offer the same feature. It is a great complementary feature to Checkm8 since Checkm8 is limited in iOS device models (iOS devices with A5-A11 Chipsets), while agent-based acquisition works even on the latest iPhones, and the supported iOS range is vast, starting with an iOS as old as version 10.
Speaking of Checkm8, Belkasoft X is adding something extra on top of the competition. For example, it can lift the so-called USB Restricted Mode—an iOS security feature that disables data transfer via a Lightning cable one hour after the latest unlock.
There are more types of iOS acquisition, such as automated screen capturing or crash log extraction, which, though limited, may give you some useful info, such as the latest IP addresses involved in your investigation.
To learn more about iOS acquisition with Belkasoft X, please watch our webinars, which are available at https://belkasoft.com/webinar. You can find recorded webinars on the Previous webinars tab, including Locked iPhone investigations, Bypassing iPhone USB Restricted Mode, and others.
Android acquisition support
For Androids, Belkasoft supports standard ADB backup creation and multiple acquisition methods based on ADB. One interesting method is our APK downgrade acquisition, which replaces an original application file (e.g., WhatsApp) with an older version. Such an older version can then be used with ADB backup creation and include much more data into our backup. This method is a breakthrough for mobile phone forensics, as it allows access to previously unavailable data. Of course, in the end, the original app version is restored.
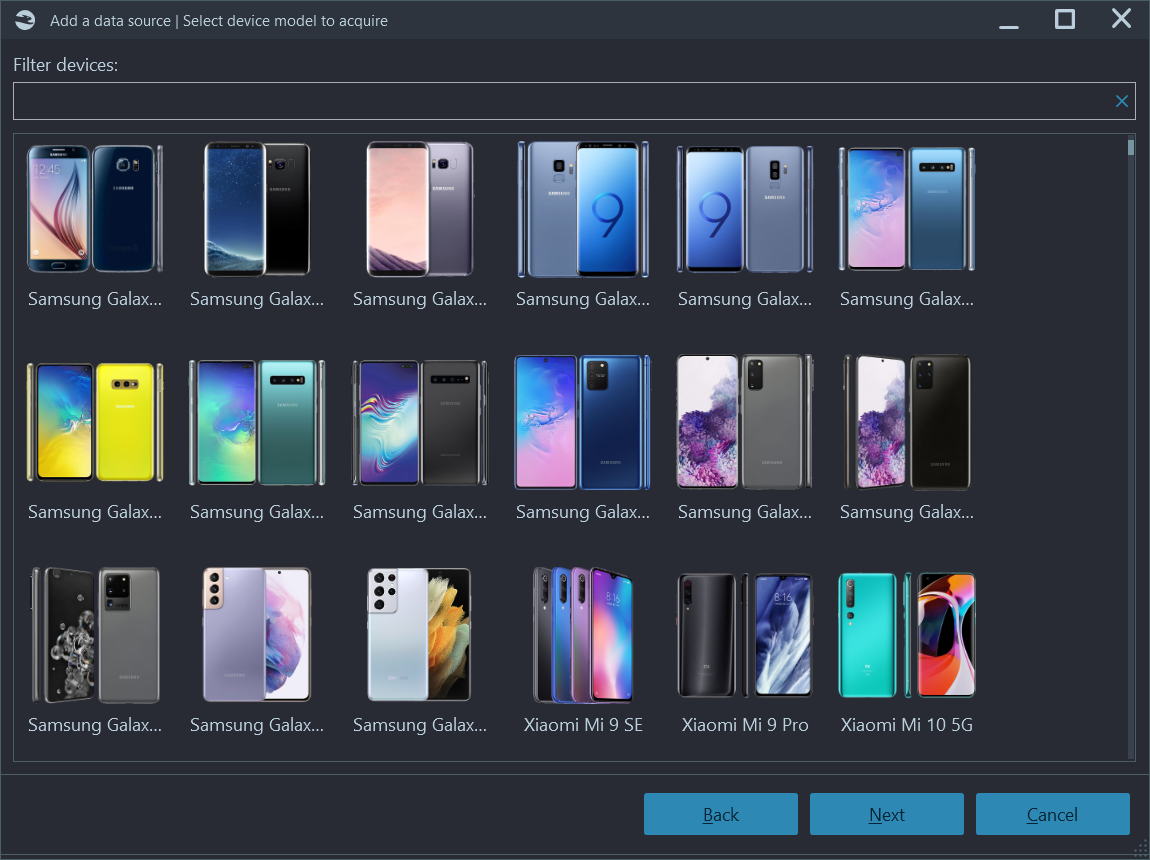
Another ADB-based method of Android acquisition by Belkasoft X is automated screen capturing. This is possibly the safest way to extract data from a device, so you may consider starting every case or acquisition with this method—before you try a riskier method. It is a key process in mobile device forensics where, as mentioned before, non-intrusive methods are often prioritized.
A new acquisition method is available for Android 12 and 13 devices that have not been updated with the Android security patch from March 1, 2024. It provides full access to application folders located under ..data\data in the device's internal file system. This approach helps bypass security limitations without needing the device to be rooted, which makes it similar to APK downgrade but on steroids.
Overall, using this enhanced app acquisition method alongside logical options provides investigators with more thorough data capture from Android 12 and 13 devices, making it easier to piece together relevant application data for forensic purposes.
Belkasoft X also supports various Android acquisition methods, specific for particular vendors or chipsets. Among them, you will find Spreadtrum-, MTK (MediaTek)-, Kirin-, and Qualcomm-based devices. For MTK, the product gives you as many as three different methods of acquisition, including two types of agent-based extraction, and Qualcomm devices are supported via the EDL (Emergency Download) mode.
The product can also acquire rooted devices and analyze TWRP extractions. It supports analysis of JTAG images and chip-off dumps and can ingest third-party images, including forensic product images and proprietary vendor image files. For example, you can analyze HiSuite backups—as well as Xiaomi images—with the help of Belkasoft X. This vast range of supported Android acquisition methods makes it highly effective in mobile phone forensics investigations.
To learn more about Android acquisitions within Belkasoft X, please watch our webinars available at https://belkasoft.com/webinar. Recorded webinars can be found on the Previous webinars tab, including Android phones investigation: data extraction and analysis with Belkasoft X and others.
SIM-card cloning
Belkasoft X also enables you to copy the entire contents of a SIM card using a hardware SIM card reader device or, for Android devices, by using the corresponding feature of the device. SIM cards often contain crucial forensic information beyond just the phone number. They include such details as subscriber identification (IMSI), network-specific data, and sometimes contacts and SMS messages. This method is integral in mobile device forensics cases where phone number tracking, message retrieval, or identity verification are key.
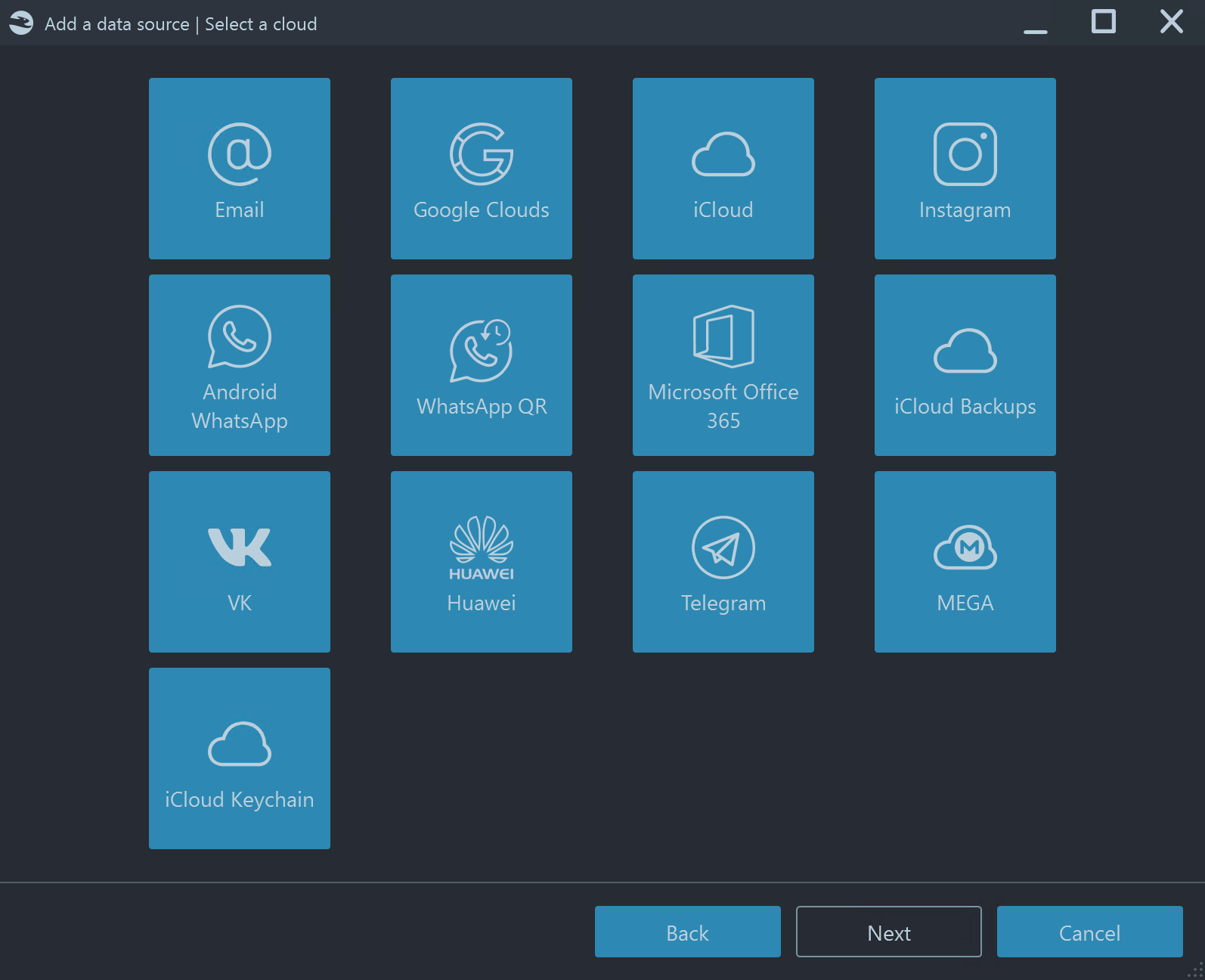
Cloud forensics
Though cloud forensics is very different from mobile forensics, performing these acquisitions can complement or corroborate data obtained from a mobile device. Since this is not the topic of this particular article, we will give two examples of useful functions in Belkasoft X, which can play a role in your mobile investigations:
- WhatsApp downloading (with or without a QR code). WhatsApp extraction is a challenging task, so every additional method you have available is priceless.
- iCloud downloading. If you cannot obtain an iPhone acquisition, iCloud can be your source of data, backed up from that device to the Apple-hosted storage
Both options (as well as many others) are available within Belkasoft X when you add a cloud-based data source to your case. Cloud data can often complement mobile phone forensics efforts by filling gaps left by device acquisition methods.
Mobile application analysis
You have now successfully imaged a device. Congratulations! Now you have to analyze the image contents.
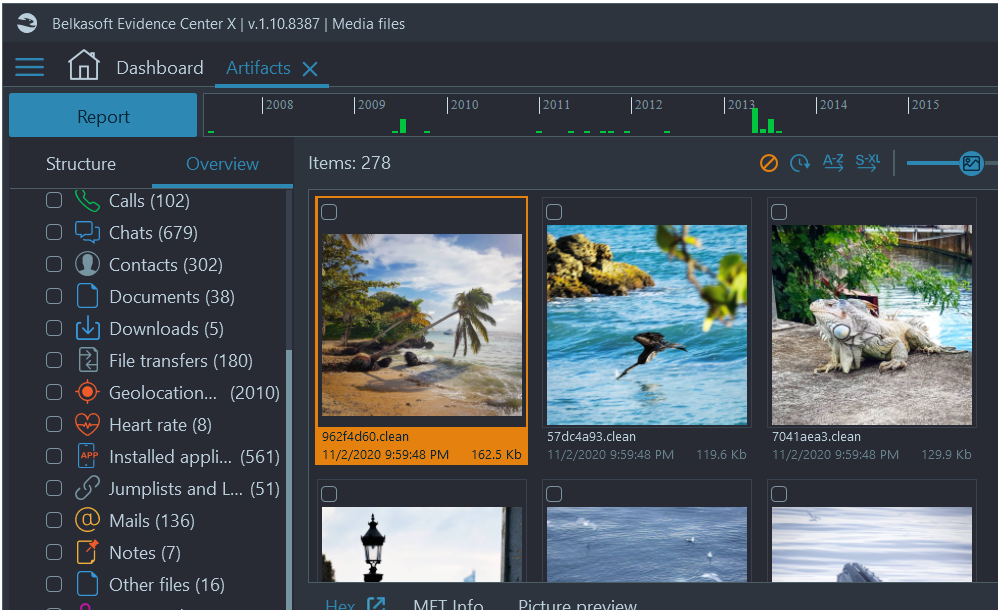
There are millions of applications available for modern smartphone users, and any automation of their analysis is indispensable to avoid growing case logs. Belkasoft X supports more than 1,500 types and versions of the most popular applications, including WhatsApp, Signal, Telegram, Instagram, TikTok, Viber, Tinder, Pinterest, and many others. Its support for automatic artifact extraction makes it a powerful ally in mobile device forensics.
While most of these apps store data in SQLite databases (SQLite analysis is another story), it is not as easy as opening your favorite database browser to extract all the data. First, a standard freeware tool such as DB Browser for SQLite (and even most forensic tools!) will not recover deleted data located in freelists, or data from WAL (Write Ahead Logs) and journal files, as well as SQLite unallocated. Second, many apps use robust encryption to prevent an examiner from opening their databases without a decryption key.
Belkasoft X can decrypt and decode multiple versions of WhatsApp—and it is not necessary to have the phone rooted! You can use our Android 12-13 method to extract the decryption key. iOS Signal messenger is another tough nut that Belkasoft X can crack once you have made a full file system extraction and captured the keychain (or if you have it from a third-party extraction).
In the user interface, Belkasoft X conveniently lays out various mobile (and other) artifacts, including audios, chats, documents, pictures and videos, geolocation data, cryptocurrency wallets and transactions, data from fitness trackers, sleep data, heart rate, etc.
Unlike other tools that often allow you to have one device per case, Belkasoft allows you to add as many devices as you need. This helps you to obtain a "bird’s eye view" via our Connection Graph—which will show how different people from your case or from different devices, were communicating. Whether it was via chats, SMS, voicemail, or calls and email, these features are invaluable in phone forensics investigations. Finally, you can make connections between your added datasets, no matter the type of device, which is a feature not supported by the competition. This can be tough and time-consuming manual work otherwise, to correlate data from a mobile device of one user with a laptop of another user, since you will have to work in two different software products, not necessarily talking to each other or supporting each other’s formats.
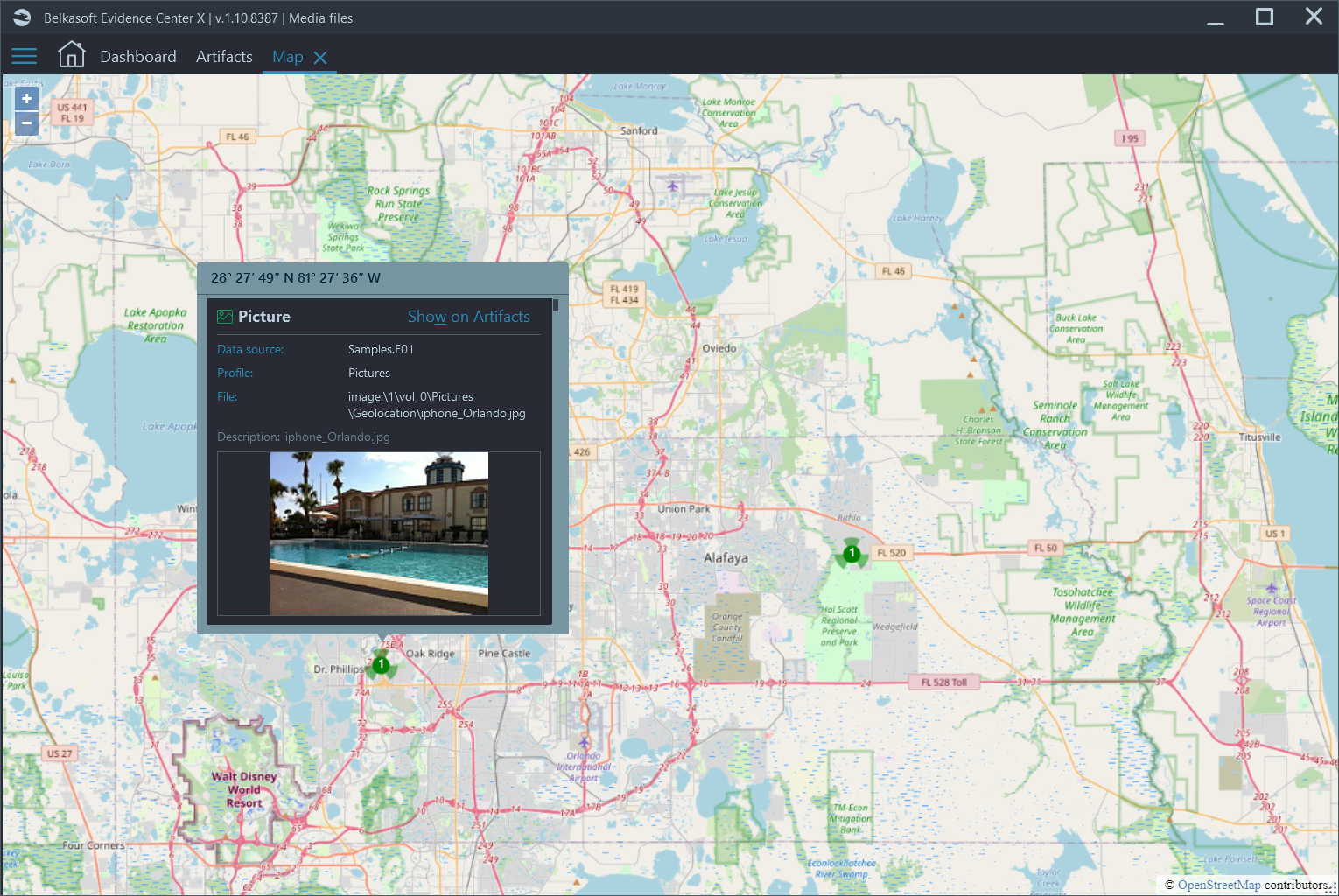
Reviewing geolocation data, such as photos made on a mobile device, with Belkasoft X's built-in Maps
Benefits of Belkasoft's solutions for mobile forensics
There are multiple reasons why Belkasoft is considered to be a tool of choice for mobile device forensics by a growing number of prominent digital forensic experts and incident responders. Among them are:
- Solid support of device acquisition, including sophisticated methods such as Checkm8 and agent-based acquisition
- A wide range of supported device models for comprehensive mobile phone forensics
- Forensically sound remote acquisition of mobile devices
- A large number of mobile applications and artifacts supported out of the box by Belkasoft X
- Very affordable price: much less than any mobile forensic software by competitors
- Perpetual, not a term-based license
Ready to test Belkasoft?
If this article convinced you to try Belkasoft tools, you can download them from https://belkasoft.com/trial. The Belkasoft X installation contains sample images with both computer and mobile data.
Do you need a more sophisticated image to try? Solve our BelkaCTF number 2 ("Drugdealer case"), devoted to an Android forensic investigation. You will see the power of Belkasoft X for yourself: even the most difficult tasks can be solved with this tool in a matter of minutes. This case is a perfect demonstration of mobile phone forensics in action, using Belkasoft’s extensive capabilities.
If you do not have the time to dedicate to a full CTF, try to catch some of our short BelkaTalk videos where we answer difficult questions from across the community, some focused mainly on mobile device forensics.
What is Belkasoft X and how is it different from other tools?
Which platforms and devices are supported for acquisition?
What are Checkm8 and agent‑based acquisition?
Can Belkasoft X deal with iOS USB Restricted Mode?
Which Android methods are available beyond standard ADB backup?
Can it handle encrypted messengers (WhatsApp, Signal)?
Which artifact types are supported out of the box?
Does Belkasoft X support cloud forensics?
Can I clone a SIM card?
How do I work with multiple devices and heterogeneous data?
Is remote (offsite) acquisition supported for mobile devices?
Can I analyze third‑party images and “non‑standard” formats?
How does licensing and pricing work?
Where can I download, watch webinars, and try the tool?
Are there training cases/CTFs to practice?
See also
- Shafik Punja's review of Belkasoft X
- Types of mobile acquisition, supported by Belkasoft X
- Six steps for mobile validation
- Android APK downgrade acquisition method
- Android screen capturing method
- SQLite forensics and why a free viewer is not enough
- Analyzing HiSuite backups with Belkasoft
- iOS Signal messenger decryption
- iCloud acquisition and analysis with Belkasoft X
- Android Viber forensics
- How you can connect mobile data with computer data in your DFIR case?
- CTF: Investigate an Android device in a close-to-real-world case with Belkasoft X
- Webinar: iOS Locked iPhone investigations
- Webinar: Bypassing iPhone USB Restricted Mode
- Webinar: WhatsApp forensics
- Webinar: Android investigation
- Webinar: WickrMe forensics
- BelkaTalk on DFIR
- Belkasoft CTFs