iCloud is a cloud platform provided by Apple for users of their iOS devices such as: iPhone, iPad and others. Particularly, it is a storage platform for various content like photos and videos, application data such as email, calendar, reminders, contacts, notes, etc. Additionally, a user may opt to store their device backups in iCloud rather than on a local computer.
This is why it is important to have the ability to download iCloud data in the course of a digital forensic or an incident response case. Data from iCloud can be complementary to what you extract from an iPhone or an iPad. In some cases, it might be the only data you can access, for example, if you do not have the device in question or if it is locked and the passcode is unknown. Moreover, since iCloud can store more than one of a user's, most recent backup, you may be able to access data which is not available even if you have the device, and it is unlocked.
In this article we will break down the iCloud data acquisition feature of Belkasoft X, a flagship software product by Belkasoft for digital forensics and incident response needs.
iCloud Forensics with Belkasoft X
Step 1: Select Type of iCloud Acquisition
First, you create a Belkasoft X case: on the Home window of the product there is a 'Create case' button that you will select. Once you have entered in the desired information and the case is created, the product will ask you to add a data source. There are a number of choices to which you can decide from: add an already acquired image, analyze a live data storage such as a hard or removable drive, perform a quick analysis (triage), and, finally, to acquire new data.
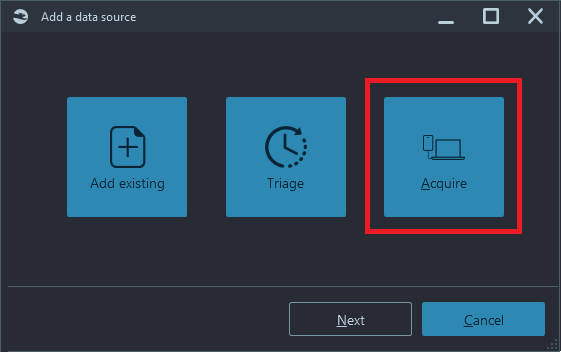
Belkasoft X supports data acquisition from computers and laptops, various mobile devices including numerous Android and iOS models, and cloud data downloading from iCloud, Google, Office 365, webmail, and so on.
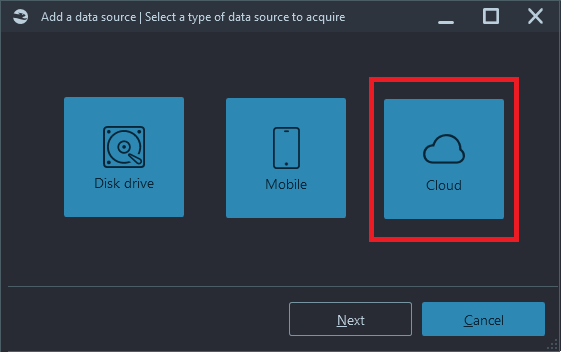
There are two methods in Belkasoft X to download iCloud data: iCloud app data and iCloud backups:
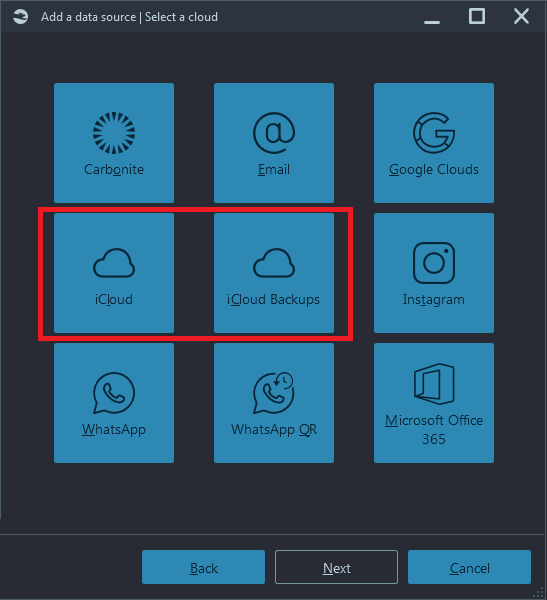
The first button ('iCloud') allows you to download photos, mail, notes, contacts, calendar and other supported types of data, which you can see above in the 'Brief Fact Sheet'.
The second button ('iCloud Backups) is devoted solely to iOS backups. These methods use different techniques and thus are separated.
Step 2: Authenticate
Clicking on 'iCloud' or 'iCloud backup' will prompt you to enter iCloud credentials. You will have to enter a valid iCloud account name and password:
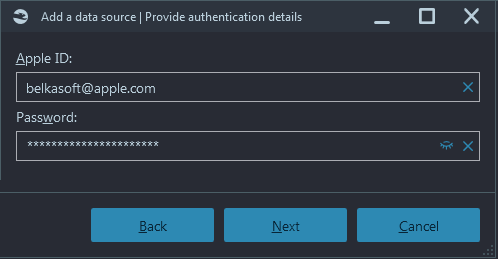
Note: Do not confuse an iCloud password with an iPhone passcode.
In the case you do not have iCloud for Windows on your investigative machine, the product will detect this and will prompt you to download the corresponding utility:
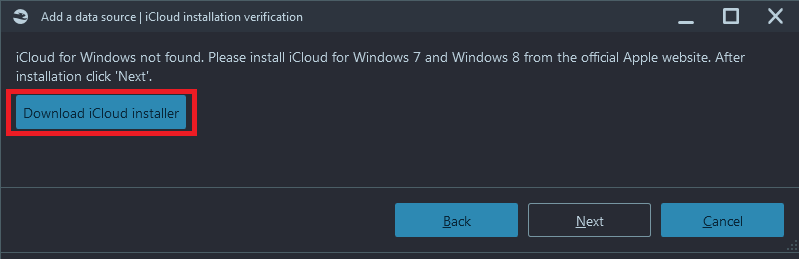
Click on 'Next' upon the installation.
What happens next depends on the account's specific security settings.
- In the case of 'one-factor' (that is, does not use two-factor authentication), the acquisition will simply start.
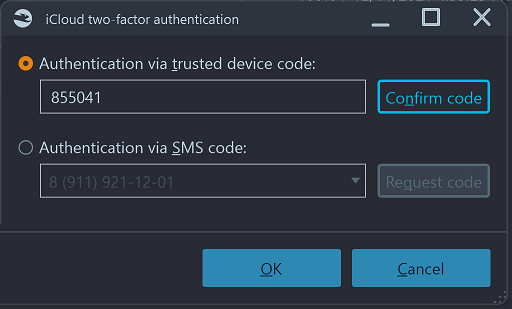
- Otherwise, you will have to enter a code received as a second authentication factor (2FA).
There are two types of second factors supported by Belkasoft X:
- SMS: A code from an SMS sent to a phone number, linked to an iCloud account
- Code: A code sent to a trusted device
In the Belkasoft X user interface you can specify which option you would like to use:
This means that you do not necessarily need an unlocked device to be able to download data from iCloud. There are some obvious cases, when you do not need it:
- If device is set to show notifications with text, you will see an SMS without unlocking it
- If two devices are linked to the same iCloud account, and you have an access to the second device, you can download the first one without even having it
What happens if you enter an incorrect code, and is there an option to guess it? You actually only have a few attempts, available for guessing the code. During our testing it was four attempts, while this number of course depends on iCloud and can change at any time. Once you have exhausted your attempts, the account will be temporary locked (verification codes will temporarily not be sent).
Step 3: Download an iCloud Backup
In this chapter we will describe the workflow of downloading an iCloud backup (in this scenario, you should click on the 'iCloud backup' button).
Once you have successfully authenticated, Belkasoft X shows you the following window:
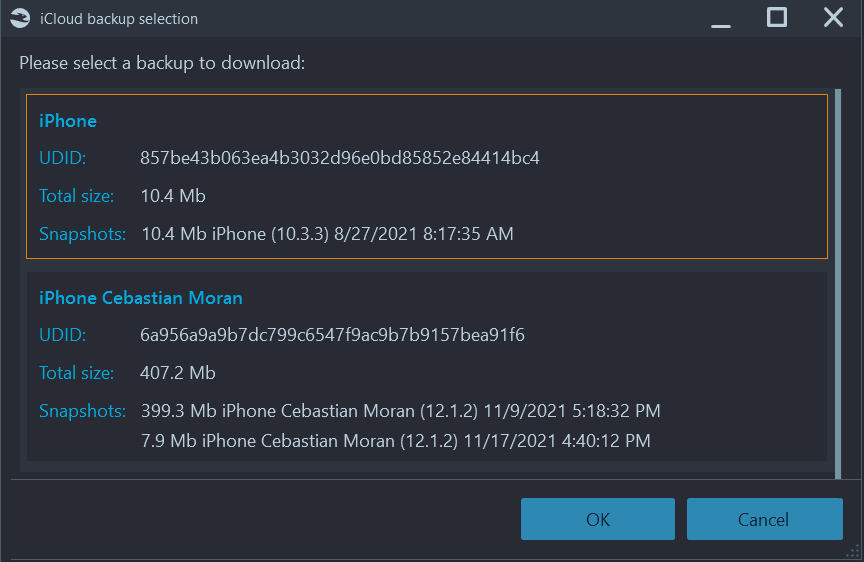
With the help of this information you can understand that the iCloud account has two backups for two different iPhones, and the second backup contains two snapshots. The backup total size is 407.2 Mb while individual snapshots occupy 399. 3Mb and 7.9 Mb correspondingly.
From the user's perspective, snapshots do not exist, they are not shown within the iCloud interface. Technically, snapshots contain only the difference between the previous snapshot and the current state of a device. This is why the first snapshot has a fair chance to be much bigger than subsequent ones.
Unlike a regular user, a forensic investigator may benefit from having some knowledge of snapshots. One important detail to note here, is the date and time of snapshot creation. This information helps to understand when a user was backing up their device. Besides, Belkasoft X can show, which piece of data belongs to which snapshot, thus giving you as an examiner, the information on the date range of file creation (if a file made its way into the second snapshot, it means that it was created in between the first snapshot creation and the second one).
In Belkasoft X, it is easy to understand which snapshot contained an artifact of interest, as snapshots are analyzed as different data sources, as shown below:
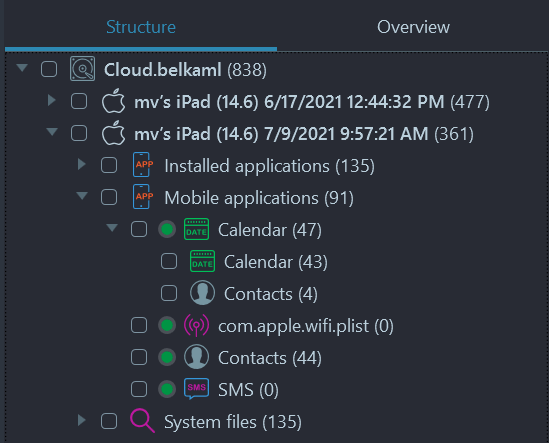
On this screenshot you can see two snapshots from the same .belkaml iCloud image
Step 4: Download iCloud Application Data
In this chapter we will describe the workflow of iCloud application data downloading (in this scenario, you should click on the 'iCloud' button).
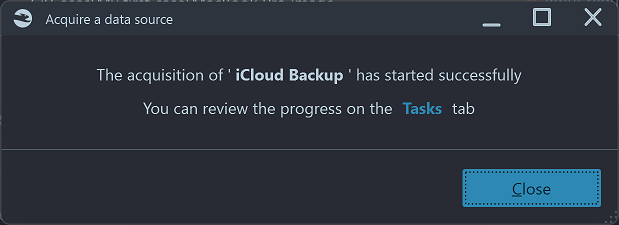
Once you have successfully authenticated, Belkasoft X will begin the acquisition. You can follow its progress in the 'Tasks' window.
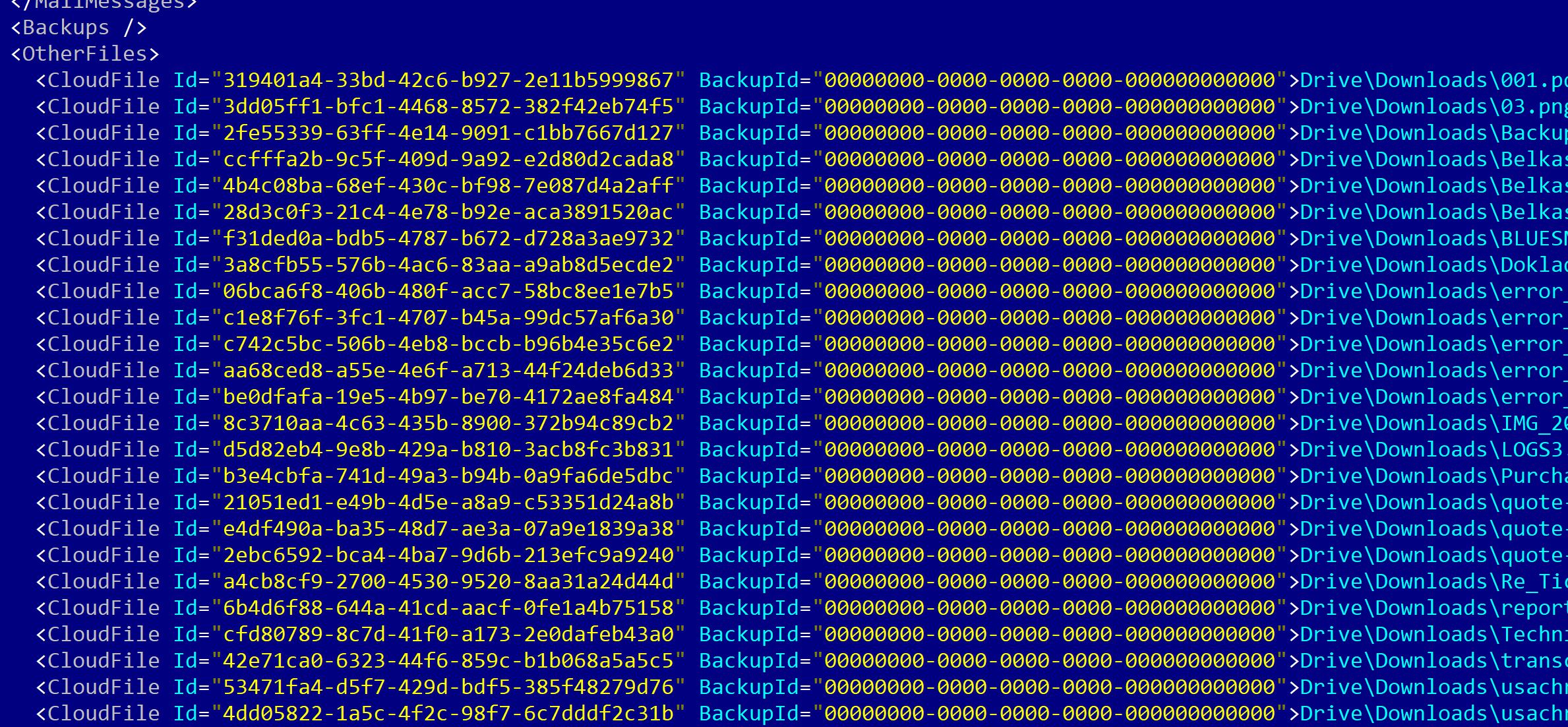
The result of this acquisition type will be saved in our standard Belkasoft .belkaml file. This is a simple XML file that contains metadata about files downloaded from any supported cloud (as well as for mobile acquisition). This file assists the examiner by adding all downloaded data to your case as a single data source. However, you can still analyze the same data with a third-party tool by just manually adding the downloaded folder to that tool. As with all data created by Belkasoft, you are not bound to our tools by tricks such as using proprietary formats—vice versa, our products use standard formats everywhere so there are no obstacles of ingesting our images to other vendors' tools.
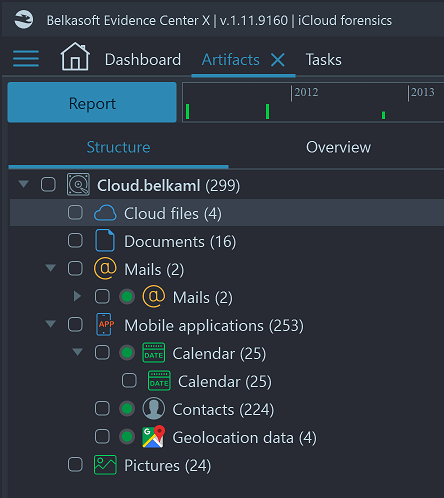
When the data is successfully acquired, it will be added to your case automatically. As a result, you can see the following artifacts, extracted by Belkasoft X out-of-the-box from the downloaded files:
Notification
It is important to mention, that unlike the downloading of iOS backups, this acquisition type leads to an email sent from Apple to the account owner's registered email address. The email will have the subject 'Your Apple ID was used to sign in to iCloud on a Windows PC'.
Conclusion
iCloud holds a wealth of user data for various iOS devices, including but not limited to iPhones and iPads. Apart from photos and various application data such as calendar, notes, and reminders, it can also contain device backups, which can be crucial for a digital forensic investigation or a corporate incident response case. Under some circumstances, it is even possible to acquire iOS device data without having physical access to that particular device. Also, you can acquire backups of all linked devices by having access to a single trusted device, bound to an iCloud account.
Belkasoft X supports the downloading of iCloud backups to include accounts protected with two-factor authentication, where no email notification will be sent to an account holder. The acquired data will be saved within a standard .belkaml file, ingested to the current case and automatically analyzed for more than 1500 artifact types supported by the product. You can distinguish data ingested from different snapshots, as they are shown as separate data sources within the product.
iCloud application data can also be downloaded by Belkasoft X. A notification is sent by Apple to the account owner. Similarly to downloaded backups, the acquired application data is saved within a .belkaml file and is automatically ingested and analyzed by Belkasoft X.
What is Belkasoft X
Belkasoft X is a software product to facilitate digital forensic investigations and corporate digital incidents handling, and it combines mobile forensics with computer investigations and cloud data examination. The product can acquire data from different devices and cloud storages, recover deleted data and extract various application details, analyze media files, detect and classify different types of photos, and so much more. The product offers both low-level forensic tools (file system viewer, hex viewer, SQLite viewer, registry viewer) and high-level ones (connection graph, graphical timeline, map, artifacts, and case statistics). It supports decryption on both whole device level and file level.
See also
- Belkasoft X Cloud forensics support
- Why Belkasoft should be your tool of choice for mobile forensics
- Media files forensics with Belkasoft X
- How to analyze different types of devices and find connections between them
- Full file system extraction for iOS devices with Belkasoft Evidence Center
Please support Belkasoft at the 4:Cast Awards 2022. Nominate Belkasoft today!
Brief Fact Sheet about iCloud Downloading
- Data types supported: iCloud backups, photos, mail, notes, contacts, calendar, find my phone info, keynote, numbers, pages, reminders, files from iCloud drive
- Which devices can be downloaded: All connected to given iCloud account
- How many backups can be downloaded: up to four per each device
- Authentication: iCloud account name and password
- Two-factor authentication support: Yes
- Types of second factors supported: SMS to trusted phone numbers, code to a linked device
- One-factor accounts support: Yes
- iOS versions: 9.0—15.1.1