Updated version of this article is available HERE
Signal is widely considered to be the most secure messaging service. Even Edward Snowden called Signal his favorite messenger app.
While the exact figures for Signal's user base are not publicly known, reports indicate that the app saw 10 million downloads in Google's Play Market in 2020, and another 40 percent of the app's users are on iOS. Signal rivals are messaging apps with larger user databases (like WhatApp, Telegram) and smaller niche messaging apps (like Wickr and Dust).
With the latest investments from Brian Acton, a WhatsApp co-founder, Signal continues to gain momentum and is becoming more popular with security-conscious users, activists, journalists, and lawyers.
The app is even recommended for use in government spaces. In February 2020, European Commission advised its staff to switch to Signal to improve the security of their communications. By 2020, over 30% of news outlets in the US, including the New York Times, Washington Post, and Wall Street Journal, use Signal to get news tips.
The core idea behind Signal is providing users with the highest levels of anti-surveillance capabilities possible. Unfortunately, such a secured app can also be used by lawbreakers as an entry point for criminal activity.
According to the annual EUROPOL report 'Internet organized crime threat assessment', these crimes might be perpetrated through instant messengers: online solicitation of children for sexual purposes, terrorist acts launched using an application as the point of communication and dark web marketplaces.
IM apps have the potential to become a rich source of evidence in criminal investigations. Moreover, when dealing with such applications, the information that can be collected in the context of an investigation goes beyond text messages.
Why is it so difficult to decrypt Signal app?
Digital forensic investigators generally struggle when they have to extract evidence from mobile devices. Specific challenges—such as different operating systems on smartphones, setbacks involving passcode recovery, and other issues—define mobile forensics.
The Signal app is hardly an exception. When dealing with this mobile app as a source of evidence, investigators should try to understand its key security features.
The Signal app stands out from its rivals with certain features, which make the app hard to crack.
1. Open source
The Signal app is completely open source. By this term, we mean that every string of code in the application can be accessed by a wide audience, anyone can audit it for errors, and people can verify that there is no vulnerable or shady code inside. For instance, code designed to gather users' data for advertising purposes.
2. End-to-end encryption
In the heart of Signal's security setup lies end-to-end encryption based on the Signal Protocol. The latter was audited by experts in cryptographic and security communities and is said to be incredibly secure. In fact, the same protocol is used in other messengers (WhatsApp, Skype, Facebook Messenger), but they are not as secure as the Signal app.
The protocol allows users to transmit messages over networks in an encrypted form. The transmitted message is then decrypted on the recipient devices only. The second layer of encryption is used for the message database. The key for this database is stored in the iPhone's keychain.
Note: What is keychain?
Keychain is the password manager Apple builds into its devices to store users' passwords, credit card details, Wi-Fi login details, and a host of other important data.
Keychain is the most popular password manager used on iPhones, so keychain extraction is an incredibly important and useful capability for any digital forensic investigator or computer security researcher to have.
The problem here is that there is no official way of retrieving keychain data. It is not extracted as a part of iTunes backup; there is no Apple-approved way to access it.
3. Other Signal features
A user can encrypt messages and notifications with a passphrase and can also use an incognito keyboard, which does not learn their typing habits. The disappearing messages function that allows people to send messages, which are then obliterated after a specific period set by them, is another useful feature.
How to extract iOS Signal data with Belkasoft Evidence Center?
1. Backups and cloud extraction
When investigating Signal conversations history on iPhones, the first idea that comes into one's mind is checking the backups. While the idea might work for some apps like WhatsApp—if the user configured the app to store conversation histories in iCloud and iCloud Drive for iOS backups—it can never work for Signal.
Signal just does not save chat histories. It doesn't keep its encryption keys in local backups. Users cannot instruct the Signal app to back up their conversations because Signal developers deliberately left out the required functions (for security reasons). If there is always nothing stored on the cloud, then cloud extraction can never be used to get Signal data.
2. Full file system extraction
Since backups and cloud extraction can't help, the other technique requires one to try a full file system extraction.
Belkasoft Evidence Center (BEC) can access the full file system from many iOS devices models through the checkm8-based feature. Evidence Center's capabilities are not limited to the checkm8-based acquisition method; Belkasoft also provides investigators with agent-based full file system acquisition. BEC can also acquire data from 'jailbroken' iPhones.
Using Belkasoft, the basic procedure for an iOS full file system extraction (with the aim of getting Signal's data) consists of these steps:
- Identify the iPhone model from which you intend to extract evidence.
Note: if you are dealing with iPhone models starting from iPhone 5S till iPhone X running iOS versions 12.3-13.4, you may use the checkm8-based acquisition method in Evidence Center. For other iPhone models, you will have to utilize the relevant jailbreak (if it exists). For older iOS versions, you can use agent-based acquisition functions.
- Open Belkasoft Evidence Center on your PC.
- Connect the iPhone to your PC with an original Apple cable through the USB 3.0 port.
- Choose the checkm8-based acquisition method in BEC.
- Enable DFU mode on the iPhone (based on the instructions BEC provided on your PC screen).
The iPhone and BEC should start communicating. BEC will apply the exploit. While the relevant operations are being executed, Belkasoft will search for the keychain file automatically.
The image acquisition task will commence. The result of the acquisition procedure gets presented as a .tar file.
Finally, when the image acquisition process reaches completion, the device will be rebooted. No traces of exploit get left on the device.
- You can now start analyzing the acquired image.
In the analysis stage, BEC will extract the Signal encryption key from the keychain and automatically decrypt Signal data.
After the iOS full file system is extracted, the 'Passwords' node will appear on the Evidence Center window.
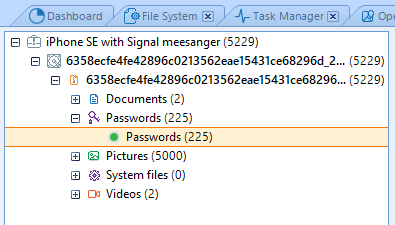
Figure 1. Password node in BEC
Passwords from the keychain file are stored either as a token or as an original character set in the Password node.

Figure 2. Extracted Signal password
The retrieved data for Signal contains chat history, calls, video, audio messages, shared images and links, and geodata, which all fall under the Signal messenger node. The latter is under the Instant messengers node in Evidence Center.
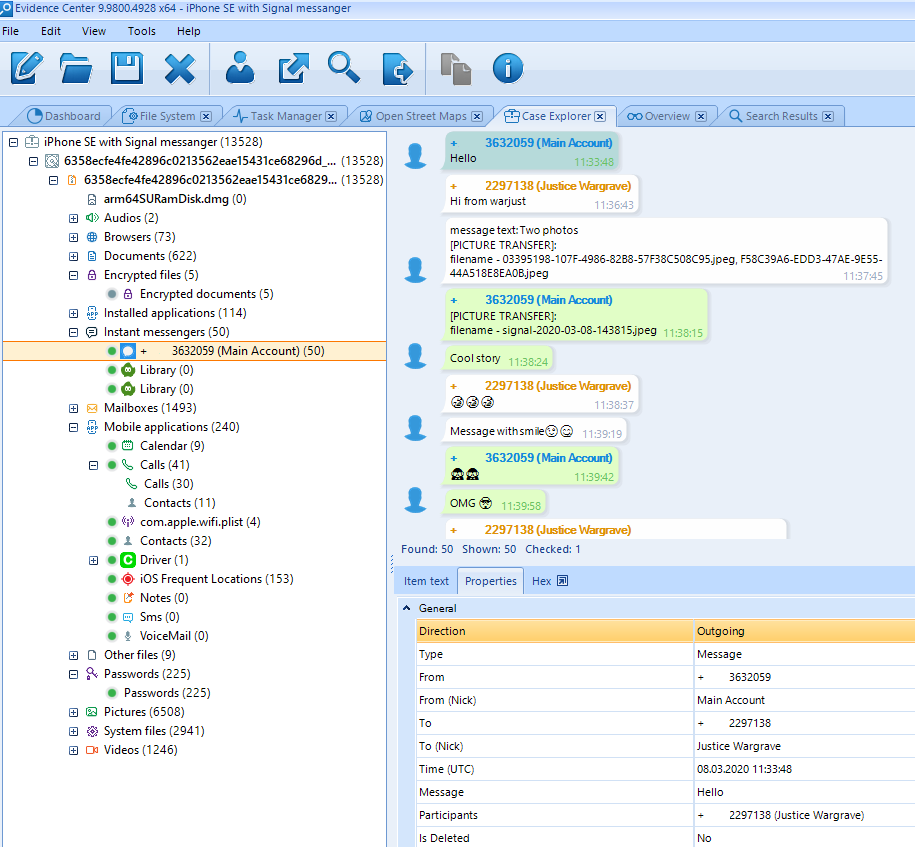
Figure 3. Extracted Signal chat history in Belkasoft Evidence Center
Conclusion
Signal is an incredibly secure messenger, which is fast gaining momentum thanks to investments from a WhatsApp co-founder. Given its impressive anti-surveillance capabilities, it already has the attention of privacy activists and officials in government agencies.
Criminals are another category of people interested in messaging apps like Signal because it provides them with top-level messaging functions and advanced protection schemes. For this reason, digital forensic investigators should strive to work with Signal as an evidentiary point. They must try to extract all its important data (chat history, images, files, etc).
With Belkasoft Evidence Center, through full file system acquisition and keychain extraction functions, an investigator or researcher can extract and decrypt communications from the iOS Signal app.
About Belkasoft Evidence Center
Belkasoft Evidence Center is a world-renowned tool used by thousands of customers for conducting computer and mobile forensic investigations. Belkasoft was named among the best and most promising digital forensics solutions by Enterprise Security Magazine—Top 10 Digital forensics solution companies 2019.
Belkasoft Evidence Center can automatically discover, extract, and analyze evidence from a wide range of sources, including computer hard drives and disk images in all popular formats, memory dumps, mobile devices, and chip-off dumps.
Since Belkasoft provides low-level access to hard disk drives and system structures, an investigator might still be able to detect data that has been deleted. With support for data extraction and analysis procedures involving Windows, Unix/Linux, Android, iOS and macOS file systems, native mounting of images created in EnCase, FTK, X-Ways, DD and SMART formats, UFED and chip-off binary dumps, and many popular virtual machines without using third-party tools, Belkasoft Evidence Center can collect more evidence than any other single tool competing in the same class.
To probe further
- Full File System Extraction for iOS Devices with Belkasoft Evidence Center
- Checkm8 Glossary
- Keychain Extraction in Belkasoft Evidence Center
- Analyzing Instant Messengers with Belkasoft
Download the trial version of Belkasoft Evidence Center at https://belkasoft.com/trial
Request a quote at https://belkasoft.com/quote