Remote Acquisition with Belkasoft R
In a digital forensic and incident response (DFIR) investigation, obtaining timely access to evidence can be a primary challenge. If devices are geographically scattered, the ability to collect data remotely is not just a convenience; it is a necessity. Belkasoft Remote Acquisition (Belkasoft R) is a powerful tool designed to meet this need, enabling swift and secure data collection from a variety of sources.
In this article, you will learn about the key functionalities of Belkasoft R, including:
- The modern challenge: Why remote acquisition is necessary
- The Belkasoft approach to remote acquisition
- Key features of Belkasoft R
- Belkasoft R remote acquisition workflow
- Cloud data collection with Belkasoft
- Use cases for remote acquisition
Read on to learn how Belkasoft R can strengthen your investigative capabilities by delivering evidence to you, regardless of its location.
The modern challenge: Why remote acquisition is necessary
The approach to digital investigations underwent a fundamental shift after 2020, when most enterprises had to shift their operations to the work-from-home model. The rise of remote work, decentralized corporate networks, and cloud services means that data is no longer confined to a single physical location. Evidence may be stored on an employee's home laptop, in a remote office, on a server in another country, or on a mobile device.
This type of data distribution poses significant challenges for traditional forensic methods, which typically require the physical seizure of devices. This approach is often:
- Slow and costly: Transporting investigators or shipping devices can result in significant delays and expenses, which hinder your ability to respond quickly.
- Disruptive: Seizing a device may disrupt business operations and alert a suspect to an ongoing investigation.
- Impractical: Physical acquisition is simply not feasible in many cross-border cases or incidents involving a large number of endpoints.
Although the need for remote data collection is clear, the process itself presents challenges. You must ensure secure data transmission, maintain forensic evidence integrity, and navigate complex network environments. These tasks require a powerful and reliable tool. Belkasoft R is designed to solve these exact problems.
The Belkasoft approach to remote acquisition
Belkasoft R is built on a straightforward, robust server-agent architecture. The Belkasoft R server is installed on your machine and communicates with lightweight agents deployed on remote endpoints. This design enables you to centrally manage and collect data from multiple devices across local and external networks for your corporate investigations.
The key principles of this approach are:
- Centralized control: Manage all endpoints, monitor acquisition tasks, and review logs from one intuitive interface.
- Flexibility: There are a variety of methods for deploying agents to suit different IT environments and investigative needs. These methods range from single-use agents for specific incidents to wider deployments via Group Policy Objects (GPOs).
- Security: SSL certificates can be used to encrypt all communication between the server and agents, ensuring the integrity and confidentiality of data in transit.
Streamlined architecture simplifies the complexities of remote forensics, enabling you to concentrate on analyzing evidence instead of overcoming logistical challenges.
Key features of Belkasoft R
Belkasoft R is equipped with a comprehensive set of features designed to meet the demands of modern digital investigations.
Flexible data source acquisition
Acquire a wide range of data types from remote endpoints, including:
- Disk drive images: Creating a full physical image of hard drives and removable devices allows you to capture all available information on the device. Such bit-by-bit copy is useful for in-depth analysis and recovering deleted data.
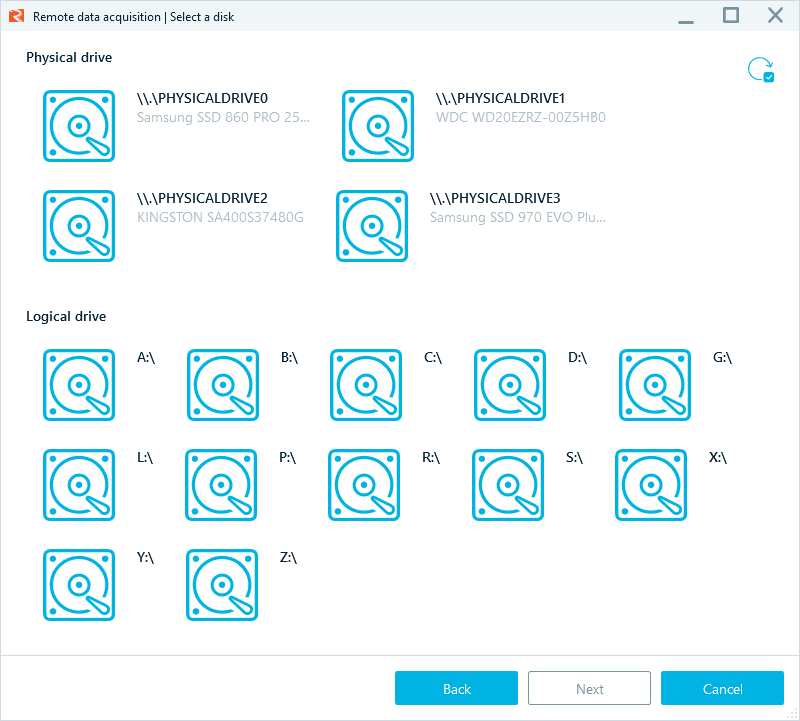
Belkasoft R allows you to acquire any physical or logical drive on a target machine
- Mobile device acquisition: Supports the logical acquisition of data from iOS and Android devices that are connected to a remote computer.
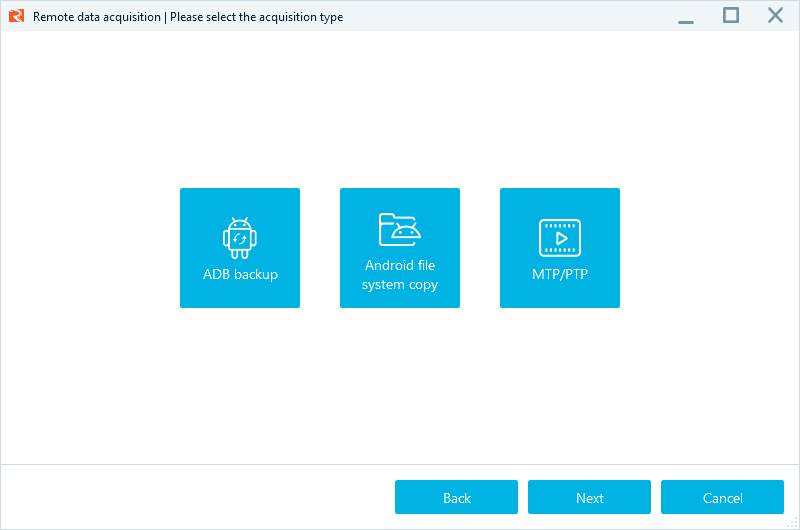
Mobile acquisition options in Belkasoft R
- Collection of specific artifacts: Enables targeted collection of specific data, such as event logs, browser histories, chat logs, and registry files, without the need to acquire the entire drive.
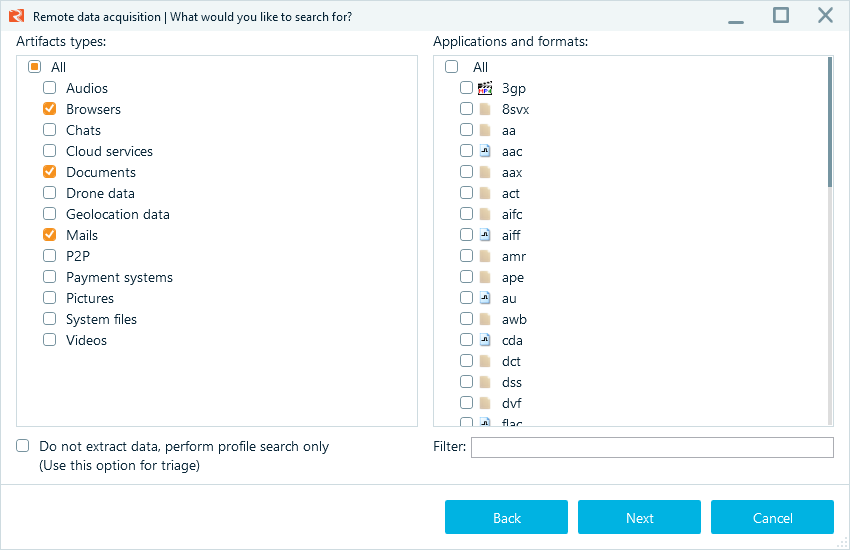
To reduce the time taken for data collection, you can specify the types and formats of artifacts to collect
- RAM capture: Captures a live memory dump from a remote machine for analyzing volatile data, such as running processes, network connections, and active user sessions.
Versatile agent deployment options
To accommodate various scenarios, Belkasoft R provides several methods for deploying agents:
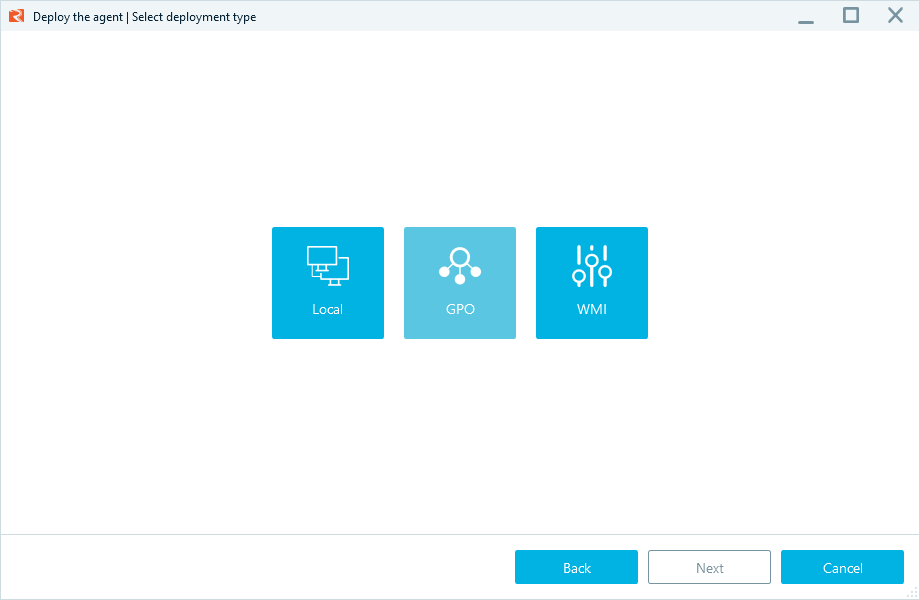
Belkasoft R agent deployment options
- Local deployment: Involves installing an agent on the same computer as the R server. Using this method, you can preconfigure agents and manually deploy them on multiple machines. This option is especially handy when technical constraints hinder remote deployment.
- WMI deployment: Utilizes Windows Management Instrumentation (WMI) for agent installation on remote machines. It is suitable for relatively small local networks.
- GPO deployment: Generates a package to install on your domain controllers to leverage Group Policy Objects for deploying multiple agents across a domain network.
A Belkasoft R agent is relatively lightweight, at around 280 MB when unpacked, which allows you to deploy it and start collecting data quickly.
Note: For local and WMI deployment, you can also use the Single-use agent option which deploys a temporary agent. This option is useful for targeted incident response, as the agent will be automatically removed after a successful data collection, retrieving used endpoint licenses.
Easy-to-use interface
The Belkasoft R dashboard consists of two tabs:
- Endpoints: Provides a comprehensive view of all connected agents and their statuses. You can specify additional information for endpoints, such as their location, inventory IDs, or descriptions to provide more context about the machines and use these values for filtering.
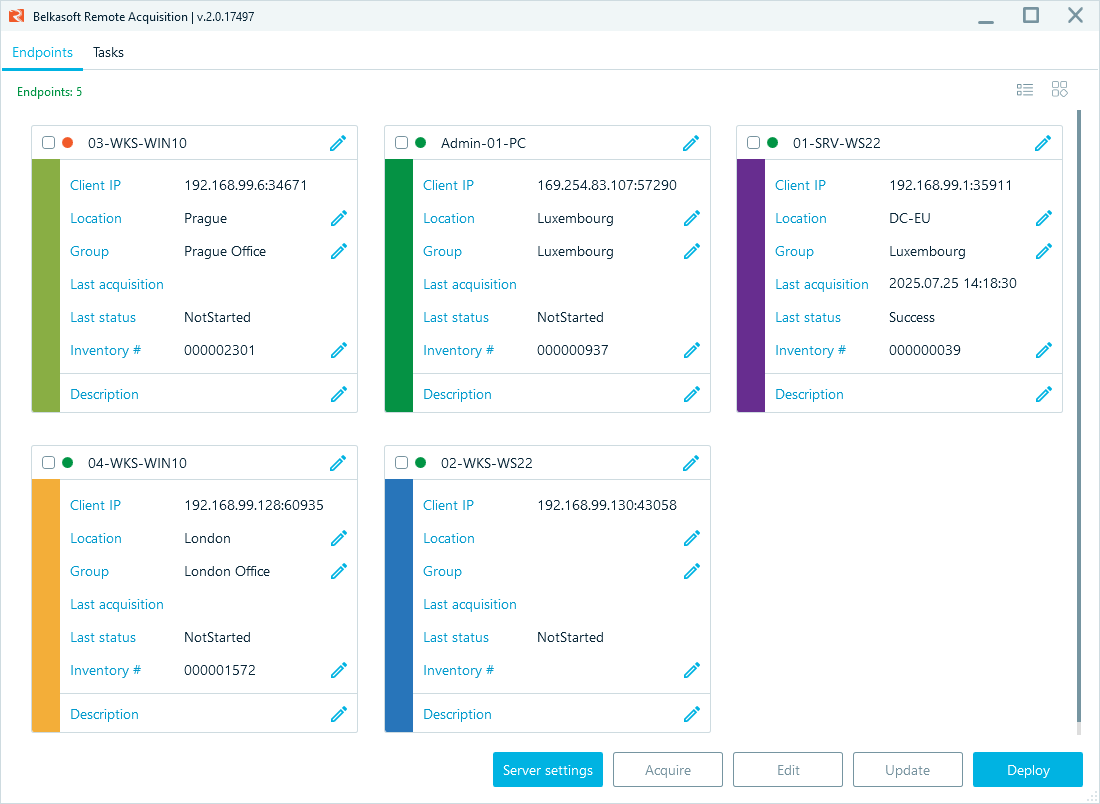
The Endpoints tab displaying the available agents
- Tasks: Allows you to monitor the progress of ongoing and completed tasks, such as agent deployment and data collection in real-time.
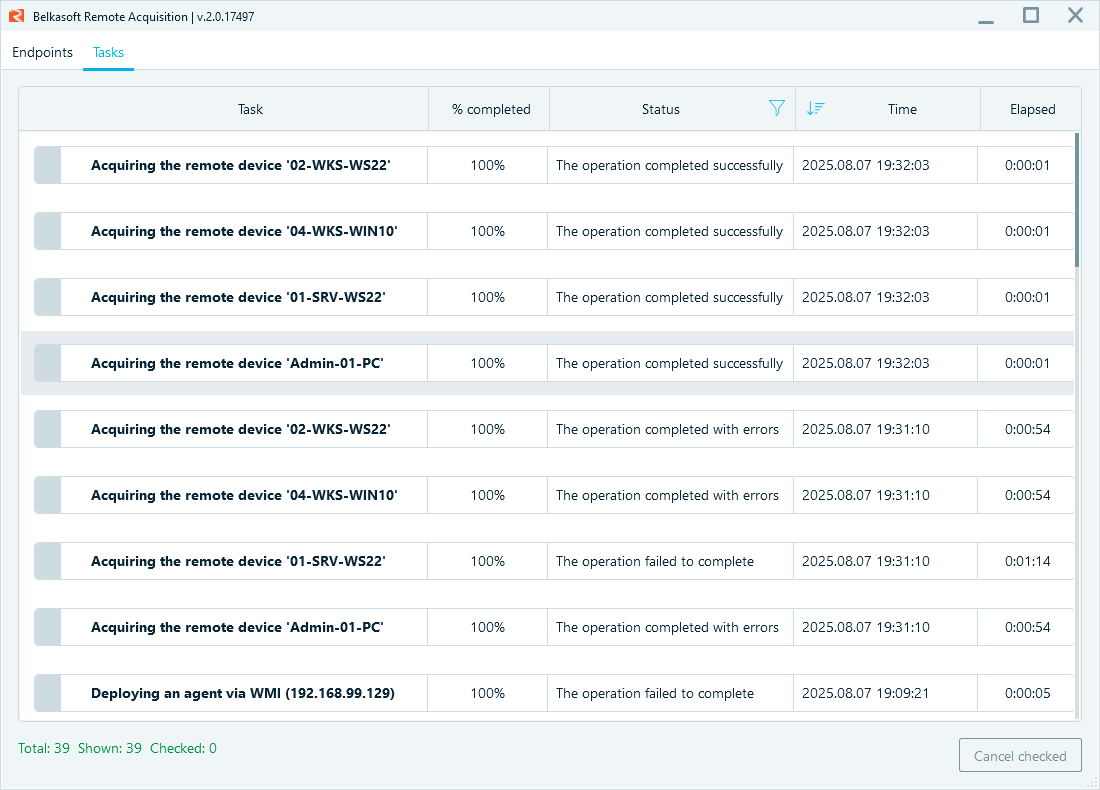
The Tasks tab with a list of completed operations
Server-agent architecture
The connection between the Belkasoft R server and its agents is direct and self-contained. It uses an embedded server that operates on the investigator's computer. This setup does not rely on external servers, allowing for deployment in networks with limited or no internet access at endpoints. The essential requirement is that the agent on an endpoint computer can establish a network connection to the server using the specified IP address and port. Belkasoft R is designed to accommodate various network configurations to achieve this connection:
- Endpoints within the same network: The server and endpoints can share a local address range, via a physical LAN or a corporate VPN tunnel.
- Endpoints on an external network: The tool supports connecting to endpoints outside of the server's address range.
- Endpoints and servers behind routers: It is also possible to connect when both the server and endpoints are behind routers. This setup requires specifying the server's external IP address and making sure the necessary port is forwarded on the router.
Belkasoft R remote acquisition workflow
The Belkasoft R process of acquiring evidence is designed to be efficient and straightforward.
1. Server setup and agent deployment
The first step is to configure the server settings, including the local and, if necessary, external IP address and port.
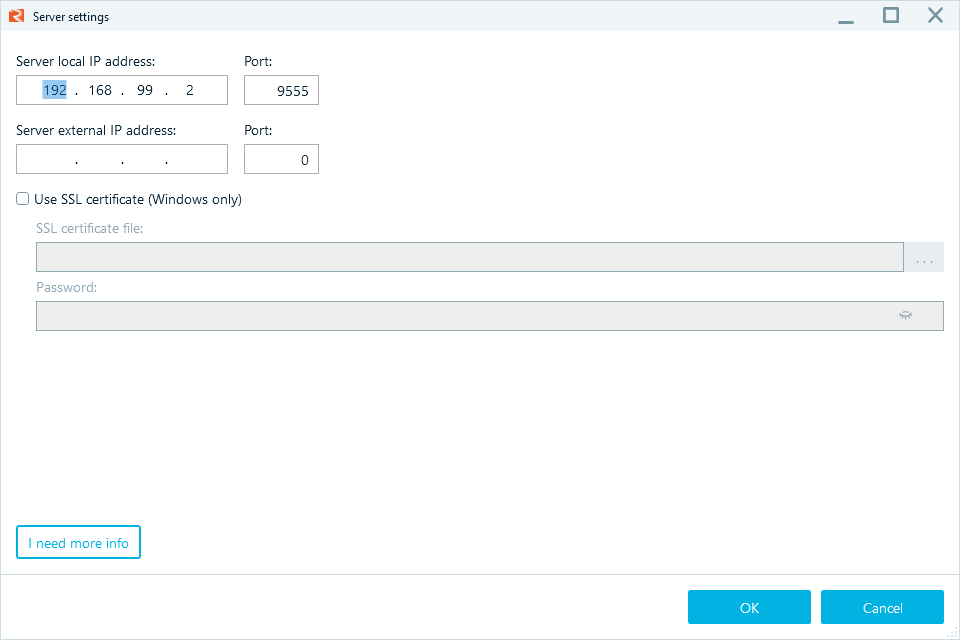
Belkasoft R server settings setup
After configuring the server, deploy an agent to the target endpoint using an appropriate method. When the agent successfully connects to the server, the endpoint will appear in the Endpoints tab with the green status.
2. Initiating an acquisition
From the Endpoints tab, you can select one or more online endpoints and start an acquisition task. The multi-agent acquisition option lets you combine several acquisition types into a single task.
Clicking the Acquire button opens a wizard that lets you select the type of data to collect.
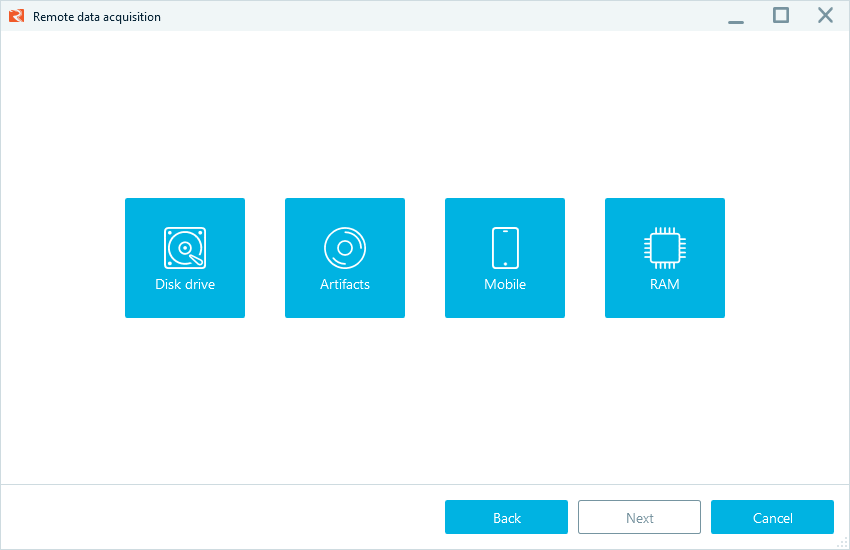
The installed Belkasoft R agent allows you to acquire drives, artifacts, mobile devices, and RAM
You can specify detailed options for each acquisition type, such as the destination for the acquired image and the use of macros for dynamic image naming.
3. Monitoring the task
After launching an acquisition task, you can monitor its progress in the Tasks tab. This view provides details on each task's status, percentage completed, and elapsed time, giving you full visibility into the acquisition process.
Cloud data collection with Belkasoft X
Corporate cyber incident investigations often involve data stored in cloud endpoints.
To accomodate forensically sound processing of such evidence, Belkasoft X enables you to acquire and analyze data from cloud services, including widely used email platforms, Google Cloud, and Microsoft Office 365:
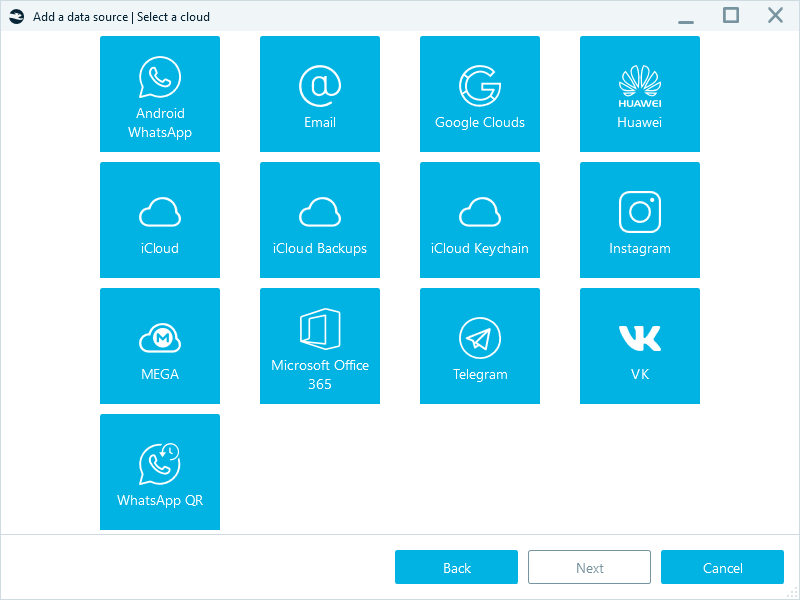
Cloud acquisition options in Belkasoft X
Use cases for remote acquisition
Belkasoft R can be utilized in various investigative contexts.
Incident response
In the event of a security breach, quick action is necessary. Belkasoft R allows you to immediately acquire volatile data, such as RAM and other artifacts, from compromised systems, eliminating the need to travel to a physical location. This rapid response capability is essential for determining the extent of an attack and preserving ephemeral evidence.
Corporate and internal investigations
For organizations with a distributed workforce, investigating incidents such as data exfiltration, intellectual property theft, and employee misconduct can be logistically challenging. Belkasoft R simplifies the process by enabling you to acquire data from employee workstations, even if the employees are working from home or in a different office, or use an employee's laptop as a proxy device to collect data from mobile devices.
Conclusion
Belkasoft Remote Acquisition is a valuable tool for any modern digital forensics and incident response (DFIR) professional. It addresses one of the most significant challenges in digital forensics and incident response by providing a secure, flexible, and efficient means of collecting data from remote devices. Whether you are dealing with a fast-moving cyberattack or a complex, geographically dispersed corporate investigation, Belkasoft R provides the capabilities you need to gather evidence quickly and effectively.

