Unlocking iOS Devices with Brute-Force
Table of Contents
Devices can be seized under various circumstances, and situations, when digital examiners do not have the passcodes to access them, are not uncommon. Such devices may stay in DFIR lab storage for years concealing crucial evidence. But you should not give up on them because brute-force methods allowing to discover device passcodes exist and keep evolving.
What is brute-force?
Brute force is a trial-and-error technique used to guess unknown information like logins, passwords, passcodes, and so on. It involves generating an array of possible values and feeding them to the input field (or screen) one by one. The more characters in the value, and the more varied they are (letters, numbers, symbols), the longer it may take to guess it.
Long and intricate passwords can take thousands and millions of years to find. However, there is always a chance that the correct combination of characters is guessed sooner rather than later, especially when employing value dictionaries that prioritize popular combinations.
How iOS device passcodes work
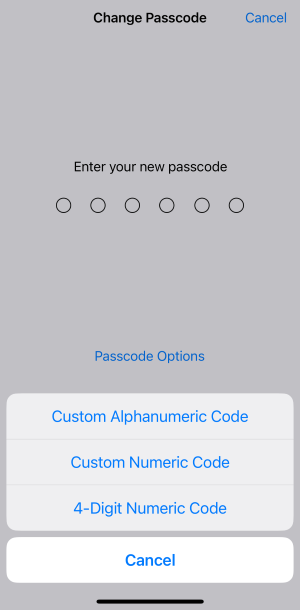
Modern iOS devices have 6-digit passcodes by default and also let users set 4-digit passcodes or custom numeric and alphanumeric values to secure their devices.
They also allow a limited number of login attempts. An iPhone or iPad gets disabled for one minute after six failed passcode attempts in a row. The seventh incorrect attempt locks the user out for five minutes, the eighth attempt for fifteen, and the tenth for an hour. If the eleventh attempt is unsuccessful, the device gets locked and can only be restored from an iTunes backup. For this reason, manual brute-force is rarely a viable option during a digital investigation.

How Belkasoft X can help
Belkasoft X includes an optional brute-force module with smart algorithms that lift the login attempt restriction and automatically guess passcodes. You can check the list of supported devices and versions on the brute-force module description page.
Here are some facts about Belkasoft's iOS brute-force:
- The algorithms support standard 4-digit and 6-digit passcodes and currently do not support custom numeric and alphanumeric ones; you can understand what type of passcode the device uses by its lock screen appearance
- The guessing speed of the tool depends on the model and iOS version of the device; the tool notifies you whether it uses the quick (3 passwords per second) or the slow (1 password per 8-9 minutes) mode when you start the process
- You can use embedded and custom value dictionaries for faster result
- The brute-force functionality is powered by the checkm8 acquisition method; if it does not work as expected, review the checkm8 troubleshooting list for possible solutions
- Be patient! Due to the complexity of the iOS device login mechanism and the nature of brute-force, it may take from a few minutes to a couple of decades to find a 6-digit passcode. To accelerate the process, you can create a passcode dictionary containing combinations of numbers that may be meaningful for the device owner, such as birthdays, historical dates, road numbers, zip codes, and so on.
How to get the brute-force module
If you are a government customer, you can request a quote for this module at sales@belkasoft.com.
Private sector customers can obtain the module as a part of X Scale edition and higher.
Conclusion
Belkasoft X brute-force algorithms assist in circumventing security measures on iPhones and iPads. While demanding some time and attention to detail, they can aid in unlocking crucial evidence.
Frequently Asked Questions
What is brute-force in the context of iOS devices?
Brute-force is a trial-and-error technique to guess unknown values (e.g., passcodes) by generating possible combinations and testing them one by one. The larger and more complex the passcode space, the longer it may take to guess.
How do iOS device passcodes work and why is manual brute-force impractical?
Modern iOS devices default to 6-digit passcodes and allow 4-digit or custom numeric/alphanumeric options. iOS enforces escalating delays after failed attempts (e.g., 1 minute after six failures, 5 minutes after seven, 15 minutes after eight, and 1 hour after ten). After another failed attempt, the device may require restore, making manual brute-force impractical for investigations.
How can Belkasoft X help with unlocking iOS devices?
Belkasoft X includes an optional brute-force module that lifts login attempt restrictions and automatically guesses passcodes. It supports standard 4-digit and 6-digit passcodes and uses smart algorithms to optimize the process.
Which passcode types are supported by Belkasoft’s iOS brute-force?
The module supports standard 4-digit and 6-digit passcodes and currently does not support custom numeric or alphanumeric passcodes. The lock screen appearance can indicate the passcode type.
How fast is the iOS passcode guessing process?
Speed depends on device model and iOS version. The tool informs whether it can use a fast mode (about 3 passwords per second) or a slow mode (around 1 password per 8–9 minutes). Actual time can range from minutes to much longer for 6‑digit passcodes.
Can dictionaries speed up the brute-force process?
Yes. You can use built-in and custom dictionaries to prioritize likely passcodes (e.g., birthdays, notable dates, road numbers, ZIP codes), which may significantly reduce time to success.
What if the checkm8-based process does not work as expected?
The brute-force functionality is powered by the checkm8 acquisition method. If issues occur, consult the checkm8 troubleshooting guidance to resolve common problems before retrying the process.
Is the process safe for evidence data?
The approach is designed for forensic workflows, but due to the complexity of iOS security, it requires time and careful handling. Follow DFIR best practices to preserve evidence integrity throughout acquisition and brute-force operations.
How can I obtain the iOS brute-force module?
Government customers can request a quote via sales@belkasoft.com. Private sector customers can obtain the module as part of the Belkasoft X Scale edition or higher.
Where can I check supported devices and versions?
Refer to the Mobile Passcode Brute-Force module description and Belkasoft X documentation to verify supported device models and iOS versions before starting.
What are realistic expectations for time to success?
Depending on the device, iOS version, and passcode complexity, the process may take from minutes to very long periods. Using targeted dictionaries can help prioritize likely codes and shorten the time to unlock.