Cyber Incident Response with Belkasoft X
Foreword
This whitepaper was prepared by Thomas Cyr from Maise, our valued customer using Belkasoft X Corporate since 2021. As part of our commitment to showcasing real-world examples, we approached professionals at Maise to share their experiences in cyber investigations and tell us what they consider important when choosing the tools to use in their work. Thomas gave us his profound perspective on incident response and explained what guided his company in choosing Belkasoft products.
Introduction
Founded in 2002, Belkasoft is one of the leading solutions in cyber incident response that assists in digital investigations of all kinds, from law enforcement to IT security. Belkasoft is known for creating products with some of the most user-friendly interfaces on the market. Their flagship product, Belkasoft X, is flexible enough to perform a variety of tasks at the highest level: from acquisition to analysis and reporting, from computer to mobile forensics.
This white paper covers some common issues and concerns regarding incident response investigations and how Belkasoft X can assist the average user in tackling them.
Where to begin a cyber investigation?
In any incident response investigation, it is important to understand where to begin. After damage control has been done and there is no immediate threat, the next step is to try and find out how the threat actor was able to compromise your assets in the first place.
There are several purposes to this step, a big one being the education of users and staff. When it comes to recovery after the fact, understanding how and why a threat actor compromised your assets eventually leads to securing yourself from the same mistake again. Knowing what you did wrong and what needs to be done to fix the issue is integral in restoring consumer faith, employee security, and reputation in your field.
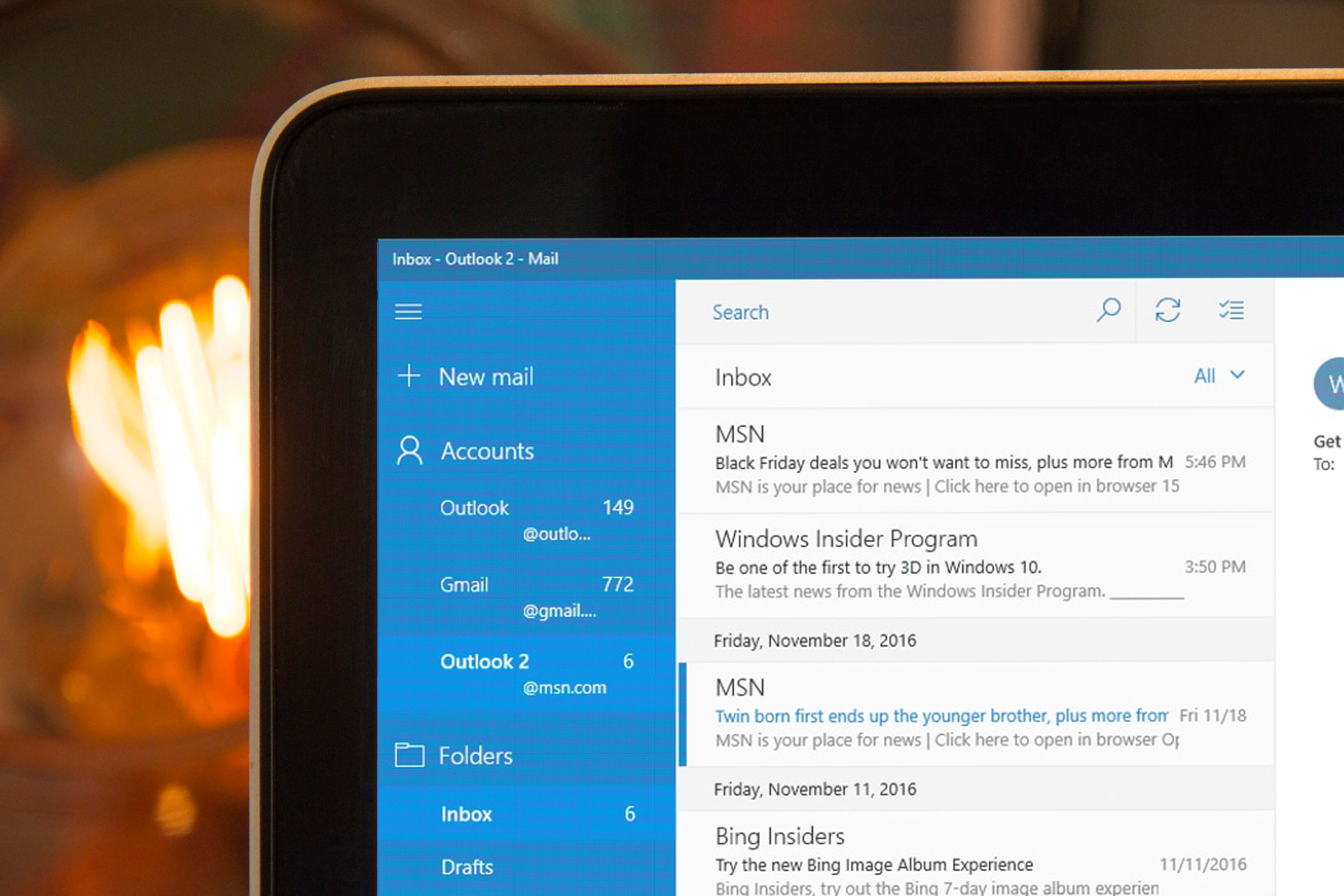
When a breach has occurred, and there is no evidence of where it started or how it happened, checking where the source of the infection most likely could be is the best option. A typical attack begins with a phishing email, and a good first step would be to check the mailboxes within the infected device. Depending on the scale, checking all mailboxes on the network may be necessary.
- Belkasoft X helps to accomplish this task. When creating a case, it is possible to choose which artifacts within the data source you want Belkasoft X to single out. Those include email applications such as Outlook, Yahoo, Gmail, and a number of others, even those that are not as popular.
- Checking for attachments in emails is one thing, but examining if the attachment was actually opened or a link was clicked by a user is another. Belkasoft X also accomplishes this by checking jumplists. This will provide information about the system files that house the details about files being opened with a click in several applications.
- Emails without attachments can still be the cause of malicious software being run on a device. This is not a challenge for Belkasoft X, as the tool can be configured to check data sources for file-sharing services such as Dropbox and other similar services popular with hackers.
Flexibility
While Belkasoft has historically been known for computer forensics, now it also provides an extensive mobile forensics tool kit. Belkasoft X focuses on iOS and Android-based devices, the most widely used mobile platforms on the market.
iOS and Android devices have different and unique backup mechanisms: iTunes and ADB (Android Debug Bridge), which can be helpful but limited in data acquisition. While riskier methods like rooting or jailbreaking exist, they are only available if you have the authority to use them.
Belkasoft X is designed to begin with the least intrusive mobile acquisition methods and, if able and necessary, will allow you to work your way up to more advanced ones:
- Belkasoft X not only supports the iTunes backup acquisition but can also use lockdown files to download device data backup if the passcode is unknown. Belkasoft X also utilizes a unique exploit within iOS devices called Checkm8, which allows you to obtain the full file system of the device and can bypass the lock screen.
- Checkm8 is restricted to iOS devices with A5 through A11 chipsets, but Belkasoft X also offers agent-based acquisition, which works on early as well as the latest models and versions of iOS devices. This agent is installed through an application and copies the contents of the file system within the device.
- Belkasoft X has a variety of acquisition methods through ADB on Android devices, such as automated screen capturing and APK downgrade acquisition. These methods tend to be specific to particular vendors or chipsets, and the number of methods available may depend on this.
Indications of attack
When it comes to hacking into a target device or network, the incident response team will look for any indication of a persistent presence. A goal that bad actors generally have is to leave a backdoor to establish a way to get back into the system if the hacker is kicked off.
Belkasoft X can not only track these behaviors but also help with persistence hunting, which is a convenient way to locate malware. Belkasoft X has a designated location within the "Incident Investigations" window where it will place persistence mechanisms.
- Startup folders hold programs that automatically start when a user logs into Windows. Run keys are the keys that force program execution. Bad actors often use these features to achieve persistence. When extracting information from your data source, Belkasoft X will automatically separate run keys into the "Startup" node and place startup folders into the "Startup folders" node. In this way, you can analyze what is running automatically when Windows boots up and detect any suspicious applications being executed.
- Scheduling a task is also a common way for hackers to develop a persistent presence. These are tasks created by the user to launch programs or run scripts and scheduled times. There are some common places where cyber attackers will place their malware, such as C:\Windows\System32\Tasks. Belkasoft X can sort these tasks by the time they were created, letting the investigator know when the malware was run.
- Services are integral to managing processes that are designed to run for a long period of time. Some of these services may run whether the user is logged in or not. Unlike other applications, services run in the background and go unnoticed by the user, which is beneficial for bad actors. Belkasoft X can show at a glance what services on the device do not look trustworthy. For example, services with strange names, paths, and creation times would be suspect to an investigator.
Attack surface
These days, in the world of cybersecurity, you will not often see a threat actor targeting just one specific computer, account, or person. When a business becomes compromised, the focus and purpose of the attack tend to revolve around how much they can control or take. It involves moving laterally throughout the system, gaining access to a large network, or acquiring privileges to access more of your data.
The good news is that when it comes to lateral movement and expansion throughout a network, a threat actor will generally be at their most vulnerable. Belkasoft X provides the ability to help an investigator detect these processes.
- A threat actor will often begin their attack by establishing a foothold on a device within the network. Afterward, however, the goal is to establish a foothold on as many devices as they can. A common technique hackers utilize is the Remote Desktop Protocol (RDP). This proprietary protocol developed by Microsoft allows one to connect to another computer over a network, view, and control it.
It is important to understand that using RDP to interact with another device is not always used for nefarious means. This feature is primarily utilized for non-malicious purposes, such as troubleshooting or administrator activities, but can also be taken advantage of by threat actors.
- It is possible to shuffle through the Event Logs to get evidence regarding RDP abuse, but Belkasoft X will make things much easier. The tool can detect outgoing RDP connections and even pinpoint the source computer's IP address, pairing it with the targets as well as the user. With the username, you can filter through events quickly and efficiently by narrowing down your search.
- Another technique used by threat actors is to utilize SMB/Windows Admin Shares, also known as a Server Message Block (Samba is a similar protocol for Linux and macOS). This is a sharing protocol for Windows machines on the same network or domain. Threat actors may look for hidden network shares accessible to administrators such as C$ or ADMIN$. This technique works best if the threat actor already has access to an account with privileged credentials. As part of your incident response plan, if you know an administrator account was compromised, you can use Belkasoft X to easily determine if there is malicious behavior regarding SMB/Windows Admin Shares.
Belkasoft X can search for keywords like C$ and ADMIN$. The "$" at the end of the share means that it is a hidden share, though Belkasoft X will still list them. If you know the specific account that was compromised, you can navigate to its registry file and look for entries with those keywords.
- Any incident response investigator understands that while threat actors are looking to gain access to one device, it is best to assume their goal is to move laterally across the network if possible. Belkasoft X will help you quickly find instances of this behavior, reducing the time spent chasing false positives.
Cloud forensics
Storing information on the cloud is becoming increasingly popular as a way of keeping data safe while also providing an efficient way of accessing it from anywhere. From scalability, redundancy, and cost-effectiveness, cloud storage is a service companies are quickly looking toward to better secure their data.

Digital forensics tends to have a poor relationship with the cloud, as these services are often hosted by a third party or offsite, making it difficult to legally acquire data needed for an investigation. This is especially attractive to threat actors wanting their digital movements to be unseen behind legal barriers. However, if the opportunity arises to legally analyze cloud data, it is imperative for digital forensics software to have the ability to properly do so. That said, forensics software must maintain pace with the current standard of applications generally used on the cloud.
- Belkasoft X provides analysis for popular cloud applications such as Google Drive, Dropbox, Flickr, and more. It can also acquire data stored in the cloud from Carbonite, WhatsApp, and iCloud, among others. Belkasoft allows you to add cloud data as a data source and analyze it in the application.
Conclusion
With the massive increase in digital crime over the last few years, it is not an understatement to say companies of all kinds and sizes are under constant attack. Experiencing a breach can irreparably damage a business, causing a loss of faith within the customer base that may never recover. With the implementation of digital forensics in an incident response plan, this loss of faith can potentially be recovered.
In this white paper, we have looked at how Belkasoft X is a versatile digital forensics tool that can view the behaviors of threat actors trying to steal your assets. Belkasoft X is very user-friendly and utilizes automated analysis methods to help investigators identify common attack behaviors. Using Belkasoft X in conjunction with an incident response plan will allow you to better learn from your mistakes and secure your systems from similar attacks in the future.
