Introduction
Digital forensic investigation is a complicated and challenging job, and it continues to become even more complex due to the rapid development of technology, including pervasive encryption, cloud storage, smartphone security improvements and so on.
It is no surprise that mistakes, which are inevitable with even the simplest routines, happen even in the course of a digital forensic (or an incident response) investigation.
In this article, we will review 5 of the most common mistakes that are often made in the field of DFIR (Digital Forensics and Incident Response).

Mistake #1: Lack of specific training
The size of a digital forensic department in a law enforcement organization or an incident response team in a corporation can vary greatly. Some can have a separate digital forensic lab and assigned digital forensic analysts and investigators, whereas others can consist of several jack of all trade's specialists, executing almost every task assigned.
With that being said, this could mean that digital forensics may be executed by a generalist who may lack specific training, for example, specialized training on a particular mobile acquisition approach.
If you think that experienced investigators and examiners are not 'vulnerable' to this mistake, that is not the case. Technology is developing at an unprecedented pace these days, and even the best knowledge of tools and methods are becoming obsolete without supportive regular training. Two years ago [as of this article creation], no one knew of the checkm8 vulnerability for iOS devices—now every DFIR specialist must know its specific language and employ this method when they meet relevant devices.
Investigators who care about staying up-to-date, usually utilize several digital forensic tools both open source and commercials. They are constantly reading books, blogs, and forums. They support less experienced colleagues—and can even learn new things by doing this.
Hint: You may also have a look at the list of books, recommended by the Belkasoft team.
Mistake #2: Lack of continuous education
Digital forensics is a very fast and ever-changing field; both investigators and criminals tend to use new technologies. That is why digital forensic practitioners should always be on the cutting edge, keep current with best practices, and be aware of the emerging industry trends. Therefore, as already mentioned in mistake #1, an expert will always need to be learning and self-educating—both on and off the clock.
What happens to those who do not learn every day? Their results become more and more incomplete. They may fail to extract new data, which is extractable with most up-to-date acquisition methods. They may brick a device due to not knowing the latest security measures by specific vendors. As a result, justice may not prevail in these cases.
Online and offline communication with fellow DFIR specialists is one of the best ways to always stay up to date. One can mention IACIS and MDFA listservs, various Discord and Telegram channels, Twitter, LinkedIn and Facebook groups—whether vendor-agnostic or vendor-specific.
Mistake #3: Use of 'push button forensics' (which is not necessarily a mistake)
The 'push button forensics' term was coined more than 10 years ago, and the forensic community considered it to be more as a sarcastic definition of digital forensic tools. In the past, practitioners resisted vendors' efforts to automate the acquisition and analysis of digital data, as they were sure that automation would make it harder to document, validate, and thus defend their science in a court of law.
Nevertheless, when hard disk drives reached the 1TB range, the Apple's iPhone emerged and changed the vision of smartphones as a gadget for good, the number of storage media devices increased (phones, gaming devices, external drives, USB sticks, and others), and most of the forensic labs ended up with long backlogs, delaying investigations.
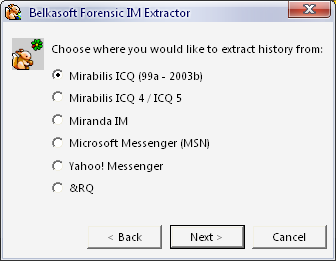
It is no longer feasible to analyze these volumes of data and to be an expert in these unbelievable number of popular applications. This is why every DFIR specialist most likely has some kind of automation in their hands now, and the artifact-based approach (by the way, first adopted by Belkasoft around 2007 in our Forensic IM Extractor) is recognized by everyone.
A DFIR tool, which allows an investigator to extract data out of the box without doing a deep dive into bits and bytes of raw data on a data source, can be considered a 'push button'. Is it a mistake to use such a tool?
The answer is both 'yes' and 'no'.
It is hard to define push button forensics as a mistake per se. Most of the digital forensic tools presented nowadays on the market are of that kind. However, there is no tool that can replace the knowledge and skills of its user. Blindly using the results of your tool's output is definitely a mistake. Knowing a tool's strengths and weaknesses, comparing the results with similar tools, repeating analysis manually in doubtful situations—is definitely not.
It is worth mentioning that some tools on the market promote using them blindly. Such tools work as a black box and give results without explanations of how they were obtained. No surprise, that conclusions based on such results will not withstand in court, if challenged by a knowledgeable counterparty. A question, which may be asked: 'How was this deleted chat restored by Software A?' could appear extremely difficult to answer, if Software A is a black box for you.
Hint: Here is how we solve this issue in Belkasoft X
A digital forensic investigator must clearly understand that no tool is a silver bullet. Even the best tool can only automate a standard routine, and once your evidence appears not to be falling under 'standard' notion, you will have to analyze it manually. Would your forensic tool find an encrypted ZIP file embedded into a PDF document, which was attached to an Outlook email? Would it find deleted SQLite records inside a memory process extracted from a memory dump?
Mistake #4: Failing to assure chain of custody and evidence integrity
Assuring chain of custody as well as integrity for electronic evidence is more complicated than for other types of evidence, such as a gun. One of the reasons for this, is that electronic data can be altered without leaving obvious traces. That is why one of the most natural questions, which the counterparty may, and will, ask in court is: 'How can you prove that this evidence (chat/document/photo) is not forged?' This is why, apart from well-known actions for preserving the chain of custody (like maintaining chain of custody forms), there are additional methods for digital forensics.
Possibly the most well-known method is hash calculation. It is good practice to calculate the hash sum for the entire data source and all files inside before doing any further analysis. Common mistakes here could be:
- Not calculating hash values at all. No further comments required.
- Using MD5 only. This algorithm is prone to collisions, and if used, must be complemented by another one, such as SHA-1 or SHA-256
- Working with the original data source instead of a secondary working copy of the image. Though this may work, if you are using hardware blocker devices, remember that SSD drives cannot be protected with such a device. Besides, software write blockers are notoriously known to not block write attempts due to errors. See also this article on many other things, which may go wrong
- Working with a cloned hard drive but forgetting to sterilize the clone. If you have not completely wiped the drive to work as a clone of the evidence drive, you can get unpleasant surprises originated from your older cases
One important factor of the chain of custody is to not only maintain the list of everyone who touched the evidence, but also to make sure that no one else had access. Since the electronic evidence exists virtually, there are more ways to occasionally allow such access, than to a gun. For example, leaving a cloned hard drive on a desk in a room, where other investigators work at the same time, breaks the chain of custody. Similarly, leaving one's computer unlocked potentially invalidates all evidence files stored on that computer.
Mistake #5: Not cross-checking a DFIR tool results
It can be a habit of the human's brain to keep doing what led to a satisfactory result in the past. In DFIR it may lead to over-using a single tool, which is relied upon too much. If an examiner is used to a particular product, they may use it even for tasks, which are not as well supported by that tool as others.
In reality, there is no single tool, which covers everything in the digital forensics and incident response domain. Even tools, which are great in a particular part of DFIR, may have glitches and issues with a particular file or an image. This is why it is always recommended to cross-check your main tool results, either manually or with a secondary product. This is why a proper toolset for digital forensics must have more than one tool for every particular area of investigation.
Relying too much on a single tool and not cross-checking results may lead to severe issues within a courtroom, whilst defending results obtained without proper validation.
Conclusion
Humans make mistakes. It is not a problem to make a mistake, it is more important how one reacts to their mistake. In the DFIR domain, where every mistake can potentially cause huge and unpleasant consequences, it is especially important to learn from already known mistakes. Learn the field. Do not stop learning even if you think you know everything. Know your tools and be able to repeat their results manually as well as explain how they were obtained. Know how to preserve a chain of custody and specifically which additional methods must be employed for digital evidence.
What other DFIR bloopers would you like us to discuss? Send your ideas and we will be happy to continue this article.
Did you like the article?
See also
- Full file system iOS acquisition on Windows with the help of checkm8
- Webinar on checkm8 with Belkasoft
- Where did this chat come from? The 'Origin path' concept in Belkasoft X
- Preserving chain of custody in digital forensics
- Why Belkasoft should be your tool of choice for Mobile Forensics
- SSD and eMMC Forensics 2016
- The Fallacy of Software Write Protection in Computer Forensics
- SANS Institute: Six steps to successful mobile validation
